Spies aren't anymore close to your vicinity. With the mobile device you have on your hand connected to the web, spies can be half way across the globe - gobbling up any information you may have, including your activities and whereabouts.
Every website you visit, your Internet Service Providers (ISPs), or anyone connected to your network for that matter, can see your browsing activity through your computer's IP address.
One solution out of a few, includes using a Virtual Private Network (VPN).
Using a VPN, you have a degree of anonymity with it masking your device's IP address from everyone.
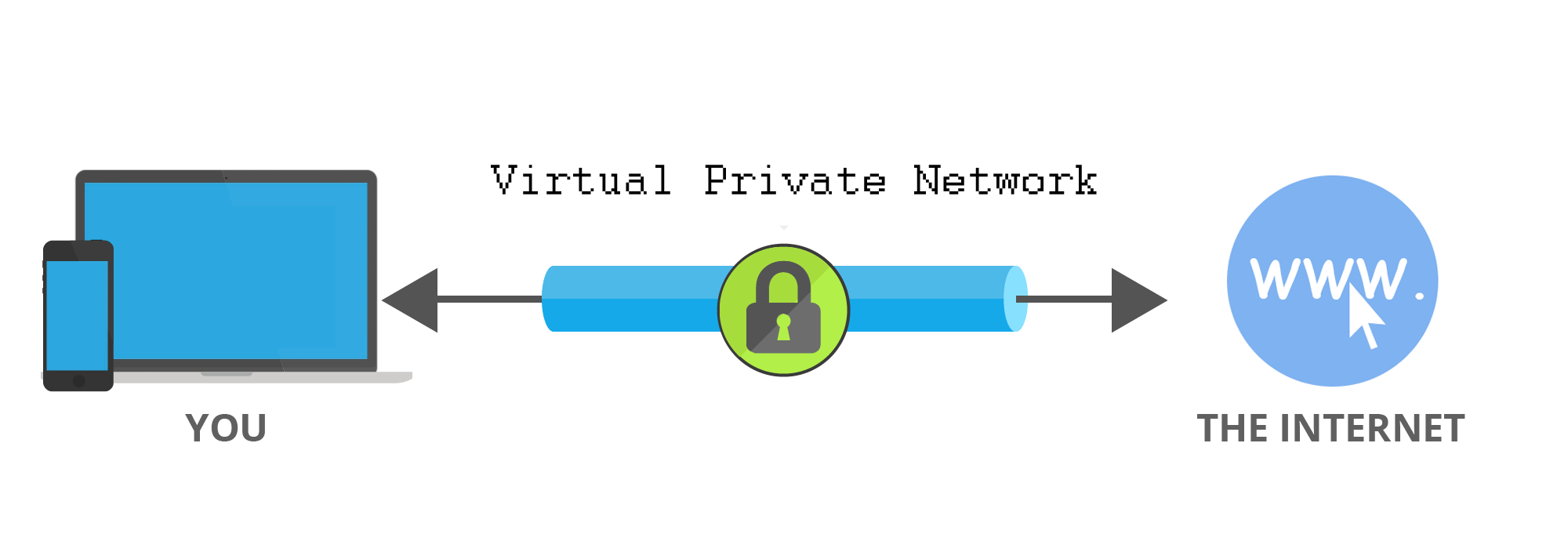
To do this, a VPN initiates a secret tunnel from your device to the internet through its network. This blocks others from spying on you.
If anyone wants to see your browsing data, they will see the VPN browsing these sites, not you.
Here, your connection and traffic are protected. But the thing is, the VPN provider can see your real IP, so it's possible for it to spy and record all your internet activity. For this particular reason, you should never fully trust any VPN provider you use.
Below is a list of things that may help you choose the best VPN for your needs:
- Privacy: For obvious reasons, you use a VPN for privacy. The first thing you need to understand, is what happens to your personal information after the VPN of your choice receives. It's recommended that the provider of your choice doesn't keep activity logs, collect or share your personal information at all. You can check this by browsing to the provider's privacy policy.
- Speed: When browsing the web, speed matters. VPN may decrease your connection speed. Here, providers sometimes publish their connection speeds, but the best way to avoid a slow service is to sign up for a trial and run a connection speed test before and after enabling.
- Capacity: All VPNs have certain amount of capacity they can give to users. Some may provide unlimited capacity, while others limit it. What you need to know here, is how much data your provider allows and whether or not your provider throttles bandwidth. When it comes to scale, bigger is better.
- Location: VPNs can be hosted in certain countries. This way you can access location-specific contents, for example. You may want to check whether the VPN of your choice has the country server you want to connect to.
- Security: A VPN tunnel can be more or less secure, and that's based on which security protocol is used. For example, you may consider using VPNs that support OpenVPN, L2TP/IPsec, strong data and handshake protection, and avoid those that use PPTP. It's also wise to choose a VPN service that maintains their own first party DNS server that won't leak.
- Payments and Communication: When you pay for your VPN service, there are many methods available, but only a few worth consideration. Services that accept cryptocurrency, cash, or misc gift cards are the best way to ensure that you are kept as anonymous as possible.
- Kill switch: Many VPN services offer this feature to prevent the device from using the internet when the VPN loses connection. This is meant to prevent accidental leaks of local connection data. Kill Switches are implemented differently from one VPN to another. A properly configured firewall should effectively secure this kill switch.

There are hundreds of VPN providers you can choose. But if you care about your privacy, and prefer to keep your personal information to yourself, it's wise to choose provider(s) considering the above criteria.
Other things you should consider, is that there are many fake VPNs out there. Preying on your trust, those fake services are meant to grab your data as it passes through. In this case, you may want to learn more about the company behind the VPN, and to know what business model it runs. It's wise to see review websites to carefully read readers' review and comments.
And if the VPN is free for you to use, you should also be cautious.
Running servers cost a lot of money, and providing free VPN service means that the company needs to make money elsewhere. Is the company behind the provider rely on its parent company? Or does it fund itself from donation or investments? Or does it have other products to sell? Learn more about them before using their service.
Then there is the country of origin.
Revelations have been made manifest regarding the mass surveillance programs of various countries around the globe. These countries are known to not only spy on their own citizens where they can get away with it, but they spy on each others, and swap information. If the VPN runs in one of these countries, it's reasonable to expect that they may be susceptible to searches and compromises made in the name of national security. In short, avoid VPNs from countries with limited internet freedom.
Security features may not limited to multihop, TCP port 443, Obfsproxy, SOCKS, SSL tunnels, SSH tunnels, and some other proprietary solutions built specifically by a given VPN company.
Don't think that no one is interested in your data. Hackers make money by grabbing and selling account information, passwords, and any other personal identifying information they can get their hands on. If you have an important information, sensitive data or communication, the more dedicated hackers may even try to use your connection to gain access to your network.
VPN is more related to security from prying eyes. If you consider better anonymity, Tor is your option.
Further reading: Staying Anonymous: Proxy, VPN Or Tor?
