Another day, another security issue found on Google Play Store.
According to a report from the security research firm Trend Micro, a number of malware apps were found stealing users' data, including banking credentials, PIN numbers, passwords, and any other information. The Android apps could even intercept text messages and infect devices with additional harmful malware.
The apps in question are essentially dropper apps.
What this means, the apps don't necessarily have malicious functions. They only serve as the trojan horse to install malicious programs, their payloads.
This is the main reason why the apps managed to pass Google Play Store's scrutiny, and managed to infect at least 7 million Android users around the world.
"Malicious actors have been surreptitiously adding a growing number of banking trojans to Google Play Store via malicious droppers this year, proving that such a technique is effective in evading detection," the researchers said.

The dropper the campaign uses, is dubbed the 'DawDropper', first discovered back in 2021. And the apps include:
- Call Recorder APK (com.caduta.aisevsk).
- Rooster VPN (com.vpntool.androidweb).
- Super Cleaner- hyper & smart (com.j2ca.callrecorder).
- Document Scanner – PDF Creator (com.codeword.docscann).
- Universal Saver Pro (com.virtualapps.universalsaver).
- Eagle photo editor (com.techmediapro.photoediting).
- Call recorder pro+ (com.chestudio.callrecorder).
- Extra Cleaner (com.casualplay.leadbro).
- Crypto Utils (com.utilsmycrypto.mainer).
- FixCleaner (com.cleaner.fixgate).
- Just In: Video Motion (com.olivia.openpuremind).
- myunique.sequencestore.
- flowmysequto.yamer.
- qaz.universalsaver.
- Lucky Cleaner (com.luckyg.cleaner).
- Simpli Cleaner (com.scando.qukscanner).
- Unicc QR Scanner (com.qrdscannerratedx).
According to Trend Micro in a blog post:
"Additionally, because there is a high demand for novel ways to distribute mobile malware, several malicious actors claim that their droppers could help other cybercriminals disseminate their malware on Google Play Store."
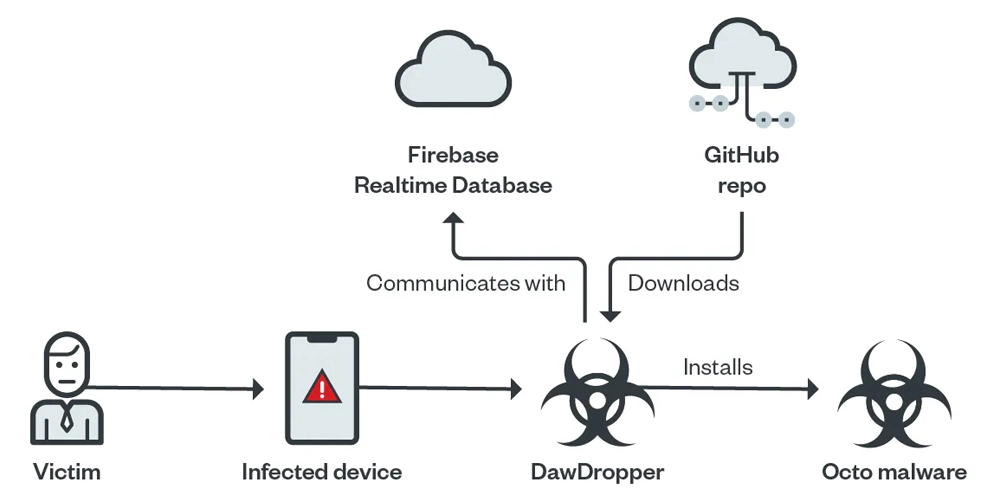
According to the researchers, DawDropper’s malicious payload belongs to the Octo malware family, which is a modular and multistage malware capable of stealing banking information, intercepting text messages, and hijacking infected devices.
Octo is also known as Coper, and it has been historically used to target Colombian online banking users.
After the researchers reached Google, the tech company quickly removed the 17 apps.
But for those who have downloaded and installed the aforementioned apps, users are urged to manually uninstall the apps immediately.
"Cybercriminals are constantly finding ways to evade detection and infect as many devices as possible. In a half-year span, we have seen how banking trojans have evolved their technical routines to avoid being detected, such as hiding malicious payloads in droppers," Trend Micro concluded.
"As more banking trojans are made available via DaaS, malicious actors will have an easier and more cost-effective way of distributing malware disguised as legitimate apps. We foresee that this trend will continue and more banking trojans will be distributed on digital distribution services in the future."
In order to stay safe from malicious apps, Android users are recommended to always check app reviews, and know who the developer is. Users should then apply due diligence when looking into app they wish to download, and always avoid sideloading apps, or downloading apps from unofficial apps stores.
