The internet is literally unsecured. Being a network consisting of networks, everything connected to it pose a threat on their own.
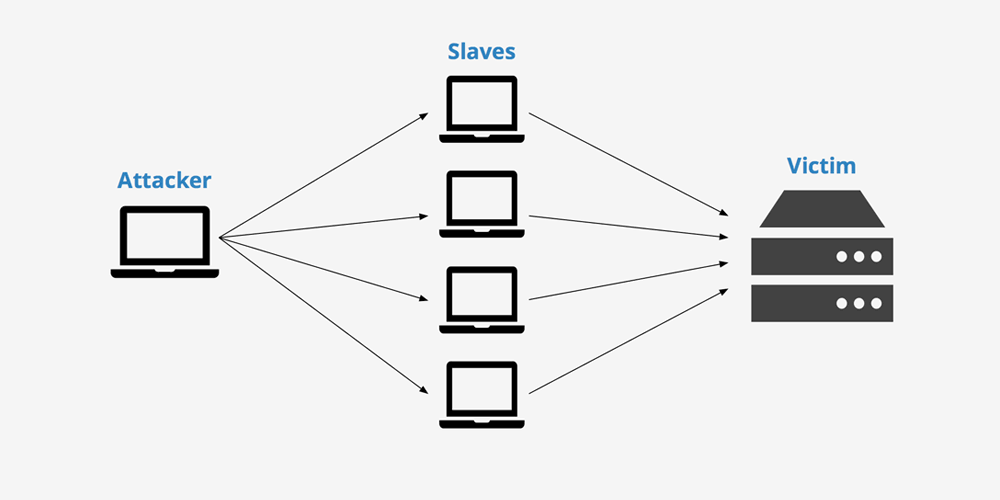
On of the ways to compromise and overload a network is by delivering it a DDoS (Distributed Denial of Service) attack. This type of attack is an attempt to overwhelm an online service with traffic from multiple sources. By flooding the machine's resources by superfluous requests, the system can be made to temporarily or indefinitely prevent some or all legitimate requests from being fulfilled. The result is the service to become unavailable.
Usually, DDoS targets variety of important resources, from banks to news websites, to even community websites or organizations.
However, with more online services are up and running, more than ever before, we're increasingly become more concerned about how poorly secured the internet is.
The IoT (Internet of Things) is seen as the thing that makes ordinary gadgets smarter that they were. But those devices, just like any other machines able to connect to the internet, are vulnerable to attacks and DDoS.
DDoS is an attempt to flood a machine with more requests that it can handle by having many other machines to work together as "slaves" or botnets, to attack it. These botnets are ordinary machines and computers as well as IoT devices that were previously infected by malicious software.
Hackers can use more than one, often thousands or even more botnets using their own unique IP addresses.
Once these machines are infected, they can be controlled remotely, even without the owners' knowledge. With many of them as slaves to the hacker, they are like armies that can be made to launch attacks to any of the hacker's desired target.
Hackers can simultaneously use to send several tens of millions of requests per second. And with IoT, there is practically no place to hide.
With the advancement of global internet availability and speed, the scale of DDoS attacks has continued to rise over recent years, even reaching over 1.1 terabits per second. That massive attack happened in September 2016 when a massive DDoS attack was carried out against France's OVH via a network of over 152,000 IoT devices that includes compromised CCTV cameras and personal video recorders.
The number of DDoS kept increasing, and there are barely any security standards implemented by companies to really secure it.
Akamai that is a content delivery network to one of the world's largest distributed computing platforms, responsible for serving between 15 and 30 percent of all web traffic. The company warns that the internet is vulnerable as it is, and because we're all using a more-than-a-decade old OpenSSH that is vulnerable to funnel malicious network traffic.
SSH (Secure Shell) can certainly be secured, just like many parts of a network and also IoT. But the trouble is that, many hardware vendors didn't want to be bothered to do so. Akamai pointed out that about 2 million devices have been compromised by DDoS, which the company called it the SSHowDowN.
What makes SSH vulnerable? The default configuration on its old versions is CVE-2004-1653, and it can be exploited by hackers to forward ports. This enables them to route malicious traffic through the device as part of DDoS command and control.
Ory Segal, Senior Director for Threat Research at Akamai, said that:
Many manufacturers of the IoTs and home routers are reusing the same set of hard-coded SSH cryptographic keys, leaving millions of embedded devices, including home routers, modems, and IP cameras open to hijacking.
Hackers are often using hacked IoT hardware as proxies to obscure their real location as they engage in criminal activity. So just like any other machines, IoT is also vulnerable to DDoS, and can be made useful for DDoS attacks on others.
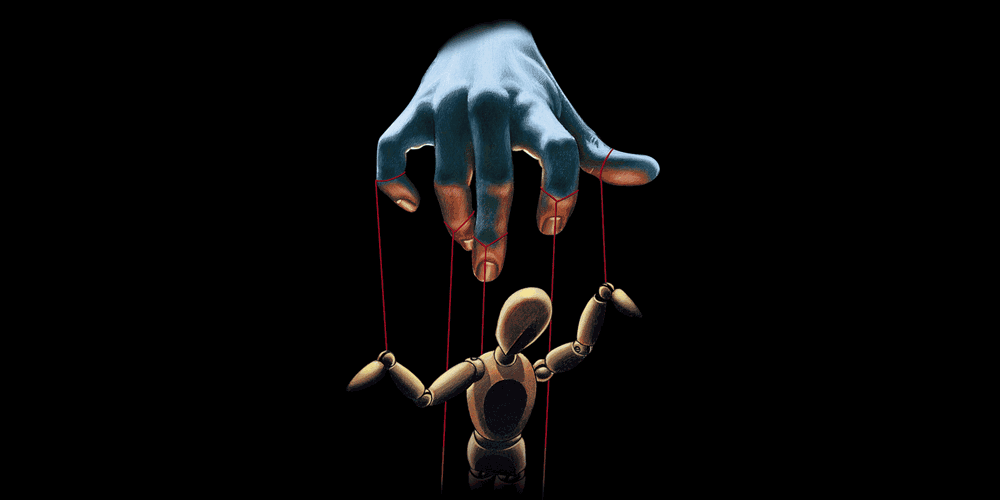
Average computers on our desks, or even IoT devices could be enslaved to do something else. So here, our WiFi-enabled home-automation system can be that "volunteer" in an army of botnets.
When our machine is infected with the malicious software to compromise it, it's becoming not our own anymore: it uses more resources that it needs, and may frequently occupied (busy and not idle) by invisible tasks we've never given it.
As more devices are getting online, firewalls and antiviruses weren't as prevalent. On average, people won't know when their computers are compromised or already enslaved by hackers to do their bidding. These hackers work in an underground community and ecosystem where experts in the fields gather to exploit and write custom software.
IoT usage will increase to become a multi-billion dollar market. With those computers coming closer to us, any form of attacks can put human lives at risk at an unprecedented scale.
It's a concern that security isn't the first thing we have in mind to secure it: we haven't yet get the necessary defense that stands to protect us from the possible not-so-smart-machines' apocalypse.
Further reading: Embracing The Internet Of Things: New Potentials Same Problems
