
Antivirus and anti-malware solutions are like watchtowers.
Their main purpose is to provide a high, safe place from which they may observe the system they are installed in. And when anything bad wants to pass, these security systems can take them down from afar, before they can do any damage to the system.
But this is where they are flawed.
According to a research from CyberArk, every major anti-malware products have vulnerabilities.
The security company tested anti-malware products from Kaspersky, McAfee, Symantec, Fortinet, Checkpoint, Trend Micro, Avira, Microsoft, Avast and F-Secure.
And here, the research suggested that all the vendors it tested could be abused and exploited to achieve privilege escalation on users' systems.
This is ironic, as anti-malware solutions are supposed to protect users but they may unintentionally assist malware in gaining more privileges on a system.
According to CyberArk's blog post, many of the security solutions have the same kind of vulnerabilities, due to their high privilege.
"The irony of abusing anti-malware solutions to increase privilege is not lost on me; anti-malware solutions that are supposed to protect the user may unintentionally assist malware in gaining more privileges on the system."
"The vast number of affected machines is troublesome; probably every Windows machine out there has had at least one software that could be abused to gain elevated privileges via file manipulation attacks."
While there are many vulnerabilities found inside security solutions, but such vulnerabilities can be easily eliminated.
And that if the security companies that make them implement several changes.
"The implications of these bugs are often full privilege escalation of the local system. Due to the high privilege level of security products, an error in them could help malware to sustain its foothold and cause more damage to the organization," the researchers said.
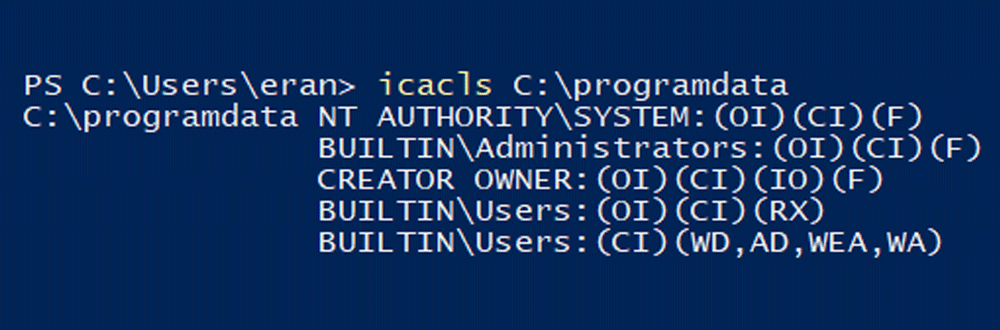
CyberArk detailed that the first cause of the many vulnerabilities found in anti-malware products came from the fact that many of them on Windows use the operating system's ProgramData directory to store data that is not tied to a specific user.
Programs that store data that are tied to a specific user generally use the %LocalAppData% directory which is only accessible by the current logged in user.
CyberArk then went out to answer two questions: first, what happens if a non-privileged process creates directories/files that would later be used by a privileged process. And second, what will happens if a directory/directory-tree is created before a privileged process?
The researchers managed to easily redirect the output of the write operation to any file they desired using a symlink attack. While the firm used Avira's product as an example, the team said that this privilege escalation method is not limited to just Avira's product.
CyberArk also found that in 99% of cases, a privileged process won't change the DACL (Discretionary Access Control List) of an existing directory.
The next common vulnerability, is DLL hijacking. By involving a standard user abusing DLL loading, malicious actors can leverage privilege by injecting code into it.
To prevent privilege escalation in anti-malware products, CyberArk recommends that the security companies change their DACLs before usage, correct impersonating, update the installation framework of their software and use
"The exploits that were presented here are easy to implement, but also easy to patch against," summarized the researchers.
