More than often, ransomware attacks hold data as hostage, and forcing victims to pay the hackers before the hackers provide the decryption key.
But the 'GoodWill' ransomware is a totally different kind of ransomware. While it does hold data as hostage, like what ransomware usually would, but instead of forcing victims to pay to the hackers, the ransomware forces victims to donate to social causes.
According to a report from CloudSEKresearchers who discovered it, the "unusual demands" the ransomware asks in exchange for the decryption key, include forcing victims to perform "three socially driven activities."
The three activities include:
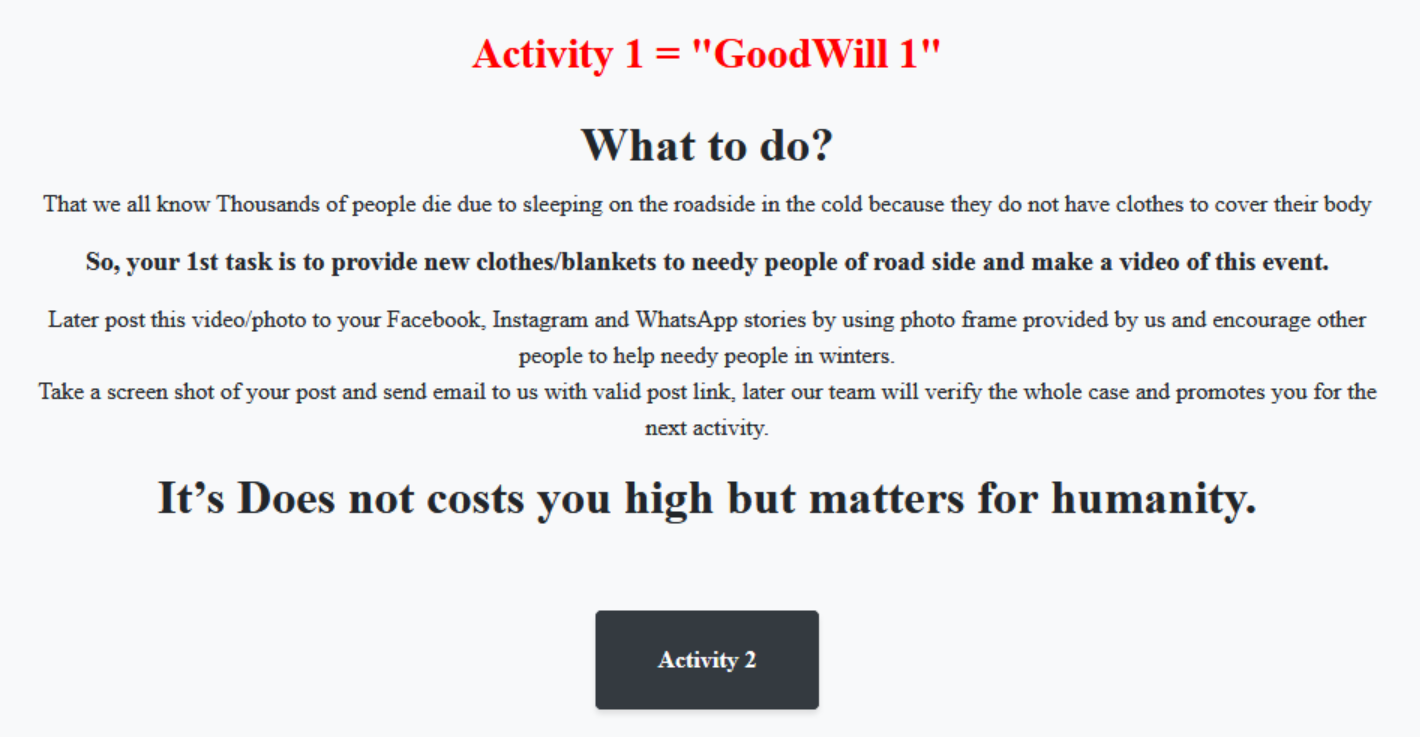
1. Donate new clothes to the homeless, record the action, and post it on social media.
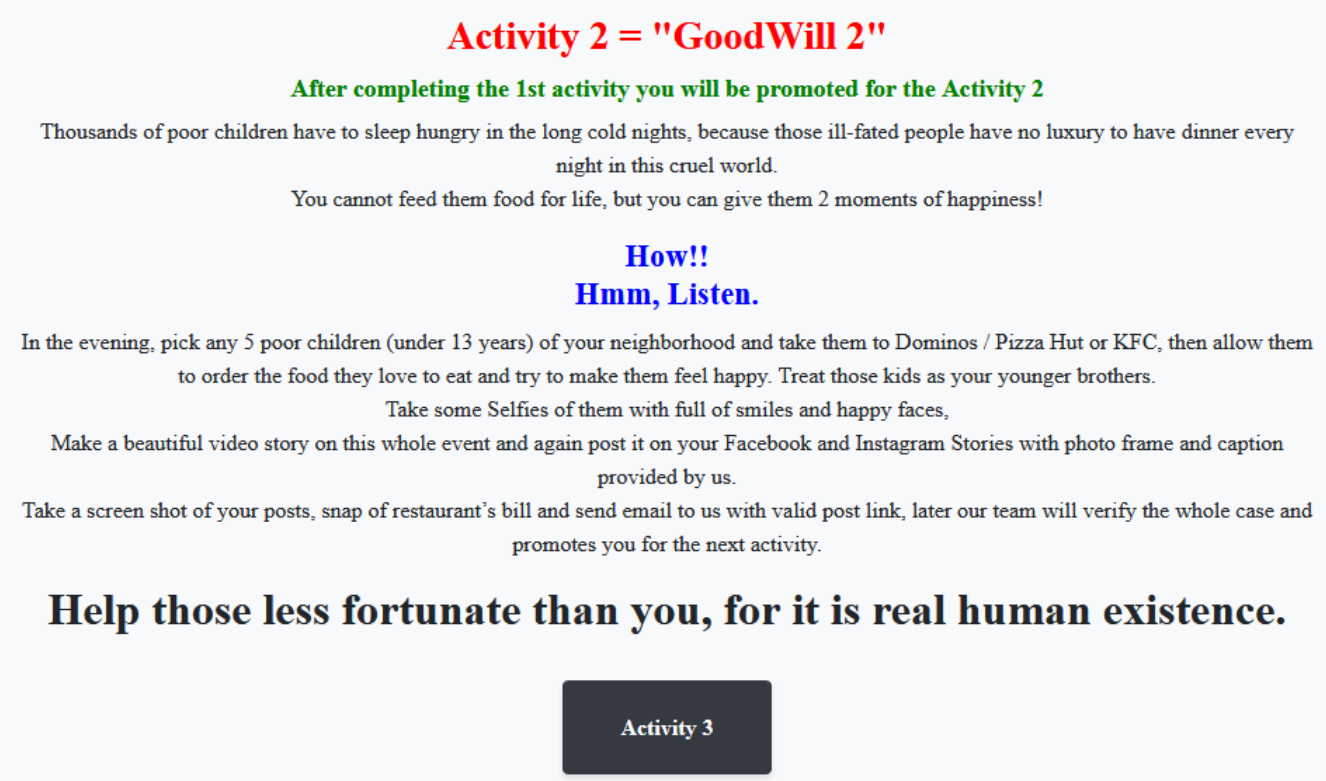
2. Take five less fortunate children to Dominos, Pizza Hut or KFC for a treat, take pictures and videos, and post them on social media.
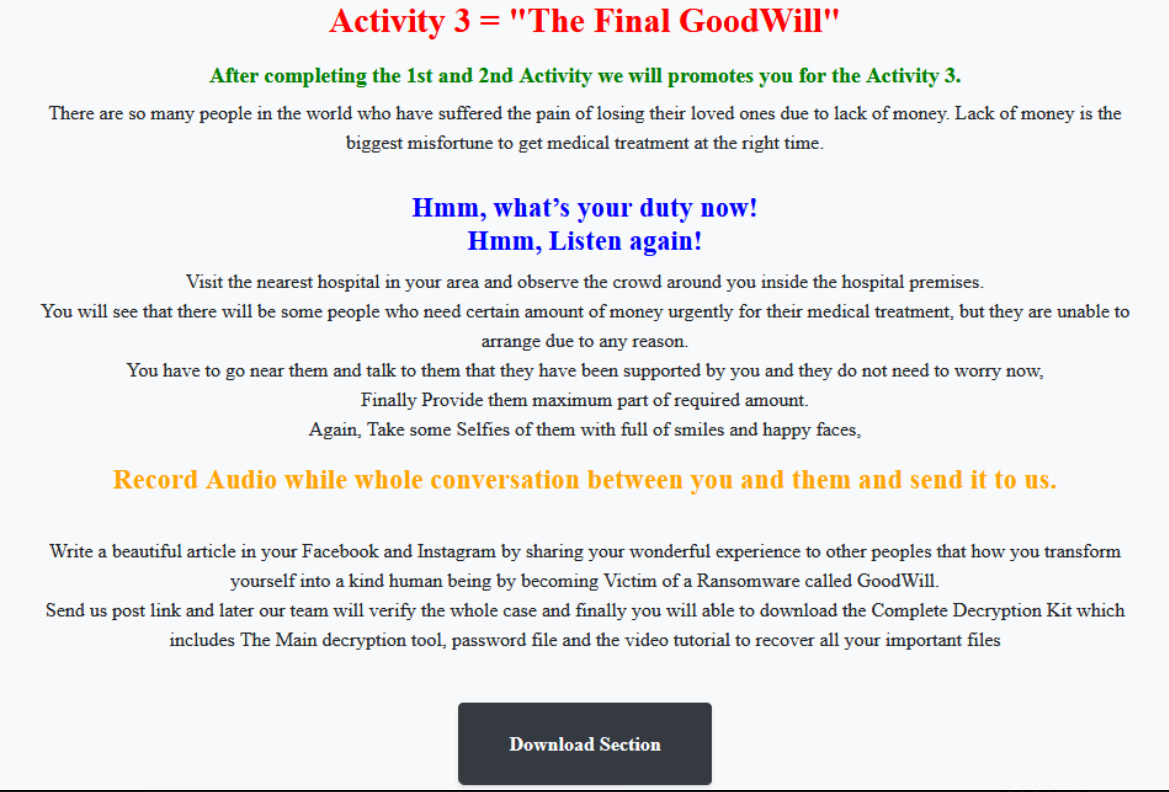
3. Provide financial assistance to anyone who needs urgent medical attention but cannot afford it, at a nearby hospital, record audio, and share it with the operators.
GoodWill ransomware was identified by CloudSEK researchers in March 2022.
When the ransomware managed to make its way to a victims' computer, it will quickly encrypt documents, photos, videos and databases. By encrypting the files, the ransomware will make the files inaccessible.
Because the ransomware encrypts sensitive files, victims could experience either or both temporary and permanent loss of data. In addition, GoodWill could also lead to a complete shutdown of operations and revenue loss of companies that have their systems infected by this malware.
And this is where the similarities end.
Unlike other ransomware variants that ask victims to pay an amount of cryptocurrencies to the hackers, GoodWill ransomware only asks victims to perform the socially-driven activities, in order to obtain the decryption key.
Making it even more unusual, the ransomware reportedly also asks its victims to write a testimonial to describe the experience that transformed them, and post it on social media.
"As the threat group’s name suggests, the operators are allegedly interested in promoting social justice rather than conventional financial reasons," according to the report from CloudSEK.
"Our researchers were able to trace the email address, provided by the ransomware group, back to an India-based IT security solutions & services company, that provides end-to-end managed security services."
