
When antivirus software are meant to secure other software, remember that antivirus solutions are themselves software. What this means, they can be vulnerable as well.
Researchers from SafeBreach Labs cybersecurity revealed a serious code execution vulnerability impacting all editions of McAfee software. The bug in question can be exploited by hackers to bypass McAfee's self-defense mechanisms.
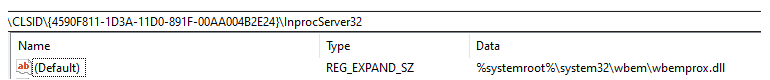
The bug existed because there weren't any digital signature validation made against the binary, and there were multiple services of the McAfee software which ran as signed processes, and as NT AUTHORITY\SYSTEM are trying to load C:\Windows\System32\wbem\wbemcomn.dll, while in fact, the file cannot be found.
When this happens, hackers can execute arbitrary code via carefully placing malicious files in specific locations protected by administrator permission, potentially leading to further attacks on compromised systems.
According to the announcement:
But for an exploit to happen, hackers need to first have the administrator privileges.
However, if this is achieved, as multiple parts of the software run as a Windows service with system-level permissions, arbitrary code execution can be achieved within the context of McAfee services.
In addition, malicious code can be set to reload each time a service is launched in order to maintain persistence on a vulnerable system.
According to the researchers, McAfee Total Protection (MTP), Anti-Virus Plus (AVP), and Internet Security (MIS) up to and including version 16.0.R22 are impacted.
Version 16.0.R22 Refresh 1 is being released to all users to resolve this security flaw.
The vulnerability was first reported to McAfee on August 5 through the HackerOne bug bounty platform. McAfee responded on August 21, before confirming the validity of the security issue on September 3.
By October 8, McAfee shared a fix deployment timescale with SafeBreach Labs, leading to the reservation of CVE-2019-3648.
