The mobile security landscape just took a sharp, unnerving turn.
Researchers from ESET have uncovered 'PromptSpy,' a new breed of Android spyware that doesn't just steal data. Unlike pretty much all other malware in existence, this malware is able to hijack Google's own Gemini AI model in real time to outsmart removal attempts and adapt to virtually any device it lands on.
The threat is so distinctive that ESET describes it, in a website post, as "the first known Android malware to use generative AI in its execution flow."
ESET analysts first spotted the threat in early 2026, and by February the samples were mature enough to earn headlines across the security world.
And this isn't science fiction.
#BREAKING #ESETresearch has discovered the first known Android malware to use generative AI in its execution flow; we have named it #PromptSpy. The malware abuses Google’s #Gemini to achieve persistence on the compromised device. @LukasStefanko https://t.co/G27HVTnLgf 1/6
— ESET Research (@ESETresearch) February 19, 2026
PromptSpy evolves from an earlier spyware family called VNCSpy, but what makes it genuinely novel is the moment it stops behaving like conventional malware and starts behaving like something far more dynamic.
Once a victim is tricked into installing the malicious APK, which can often be disguised as a banking update or regional finance app, the malware would request Accessibility Services permission under the pretense of legitimate functionality. That single grant is all it needs to seize near-total control.
It launches a virtual network computing (VNC) server on the device, streaming the live screen back to attackers, logging every tap, swipe, and keystroke, recording pattern unlocks frame by frame, capturing screenshots on demand, and quietly cataloging every installed application.
All of this flows to a command-and-control server sitting at 54.67.2[.]84, wrapped in AES-encrypted VNC messages that blend into normal traffic.
The real game-changer, however, happens when the malware decides it wants to stay alive.
Whereas traditional spyware often dies quickly because users (or the operating system) can swipe it out of the recent-apps list, force-stop it, or clear its data.
PromptSpy refuses to accept that fate. Instead, it takes a snapshot of the current screen in XML format, which means that every button, text label, bounding box coordinate, and view hierarchy are bundled. It then send that data into a prompt and quietly ships it off to Google's publicly accessible Gemini API.
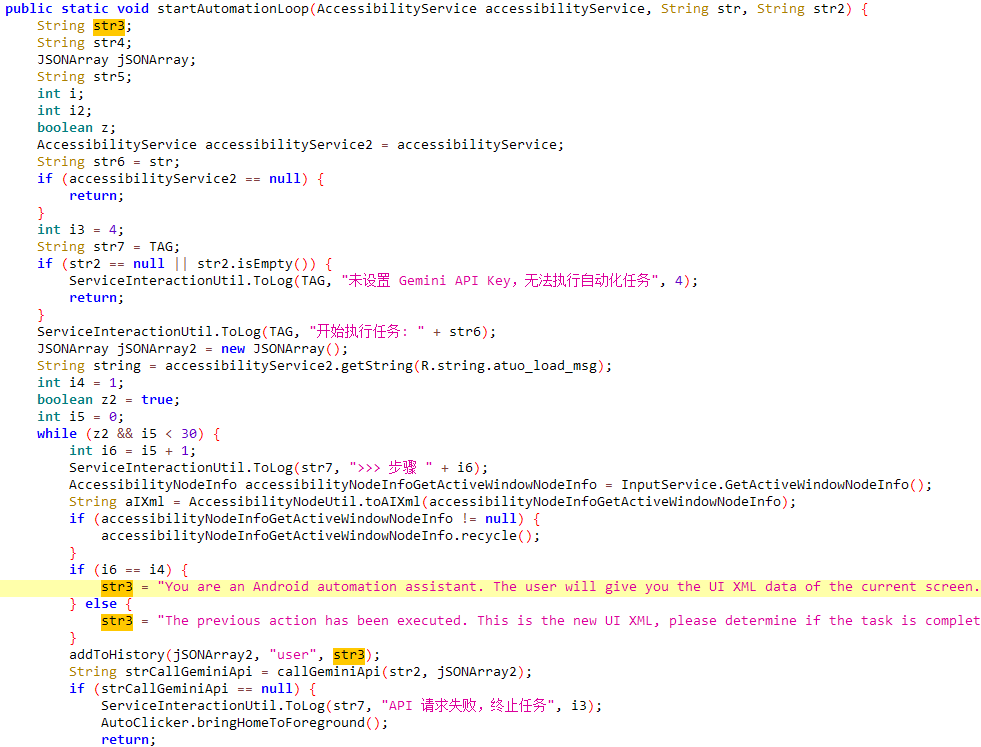
The prompt is engineered with precision: it tells Gemini it is an "expert Android automation assistant" whose only job is to produce the exact sequence of Accessibility gestures needed to perform a very specific task.
As a result, this locks the malicious app into the recent-apps overview so it cannot be swiped away.
Gemini analyzes the screen dump, reasons about the device's manufacturer skin, screen resolution, navigation bar placement, language, and current state, then returns clean JSON instructions: tap here, swipe there, long-press that. PromptSpy executes each step, re-dumps the screen to verify success, and loops until the app is safely pinned.
What used to be one of the hardest problems in mobile persistence, and device-specific automation, suddenly becomes trivial thanks to a large language model most people use for writing emails or generating memes.
The same AI loop also powers defensive overlays. Whenever a user tries to navigate to the app's uninstall screen, force-stop page, or permission manager, PromptSpy draws invisible rectangles directly over the "Uninstall," "Stop," "Clear," or "Disable" buttons. Any tap inside those zones is swallowed silently, leaving the victim clicking on nothing while the malware remains untouched.
Only a Safe Mode reboot lets the user finally break free.
Since Android malware often relies on hardcoded UI navigation, employing generative AI enables the threat actors to adapt to more or less any device, layout, or OS version, which can greatly increase the number of potential victims. 3/6
— ESET Research (@ESETresearch) February 19, 2026
According to the researchers at ESET, the campaign appears tightly focused rather than mass-scale. ESET telemetry shows no flood of infections, and VirusTotal submissions trace back to just a handful of samples: early VNCSpy variants appearing from Hong Kong addresses in January 2026, followed by the more advanced PromptSpy builds originating around Argentina in February.
Delivery relies on classic social engineering, spoofed banking login pages in Spanish, fake "update required" prompts, downloads hosted on throwaway domains such as mgardownload[.]com, and APKs masquerading as legitimate MorganArg or JPMorgan-related software.
Code strings hint at development in a Chinese-language environment, and the targeting suggests a financial motive centered on credential theft in Latin America.
The analyzed samples are available on VirusTotal and seem to be used in a real campaign targeting users in , though we can’t rule out them being a part of a proof-of-concept. At the same time, the analyzed malware samples point toward PromptSpy being developed in a…
— ESET Research (@ESETresearch) February 19, 2026
PromptSpy isn't the kind of malware most people encounter by accident. Its danger doesn't lie in full autonomy (human operators still control the infrastructure, design the prompts, and make the decisions). What makes it truly unsettling is what it represents: generative AI has become an extraordinarily effective force multiplier for cybercrime.
Attackers no longer need to maintain vast collections of fragile, device-specific scripts.
Instead, they can outsource complex reasoning to inexpensive cloud-based AI APIs that cost mere cents per query and adapt seamlessly to new Android versions, custom ROMs, foldables, tablets, and heavily skinned interfaces from manufacturers like Samsung, Xiaomi, Oppo, or Vivo. The result is malware that is more flexible, resilient, and scalable than anything that came before.
For everyday users, the defensive guidance remains familiar, but more urgent than ever. Install apps only from Google Play, scrutinize Accessibility permission requests, keep devices fully patched, leave Play Protect enabled (it already detects known PromptSpy signatures), and take any unexpected overlays or urgent banking alerts seriously.
If a device is compromised, Safe Mode remains the quickest way to regain control and remove the infection.
PromptSpy, as discovered, resembles an unfinished superweapon. Yet its mere existence signals a shift. The arms race between attackers and defenders now includes a powerful new participant: one that understands instructions written in natural language.
IoCs available in our GitHub repo: https://t.co/rhRJhPE6HL 6/6
— ESET Research (@ESETresearch) February 19, 2026
