Apple has one of the most secure ecosystem in the commercial tech sphere, and the way its operating systems work can be considered beyond the leagues of others.
In the malware and hacker-ridden digital world, people have long believe that every device needs an antivirus software. But that's not true for iOS devices. This is because the operating system considers antivirus apps like any other apps, in which they should work in a contained sandbox, preventing them from interacting with other apps.
The way iOS works essentially prevents antivirus from working properly.
The same thing happens with malware, as malicious software cannot cross the sandbox it is put into.
Apple's iOS doesn't allow apps to do such thing in its system, because it's designed to deeply separate apps from the rest of the system. This also prevents apps or anything else from gaining the permissions they need to do any significant change.
And if ever malicious codes managed to sneak in, a simple reboot should clear everything.
This is one of the reasons why Apple's mobile devices don't need antivirus software.
But the 'NoReboot' is sneaky.
Discovered by researchers at mobile security firm ZecOps, NoReboot is a bug that worrisome due to its ability to remain persistent.
The researchers found that the it can block, to then simulate an iOS rebooting operation, in order to deceive victims into believing that their phone has been powered off when, in reality, it's still running.
The bug essentially allows the tampering of the routines used in iOS to shutdown and restart the device.
In this case, the bug is able to give the impression that the device has been shut down without shutting it down, by allowing the hijacking of the event that's activated when users simultaneously presses and holds the side button and one of the volume buttons, and drag the "slide to power off" slider.
In a blog post, the San Francisco-headquartered company called this NoReboot the "ultimate persistence bug […] that cannot be patched because it's not exploiting any persistence bugs at all — only playing tricks with the human mind."
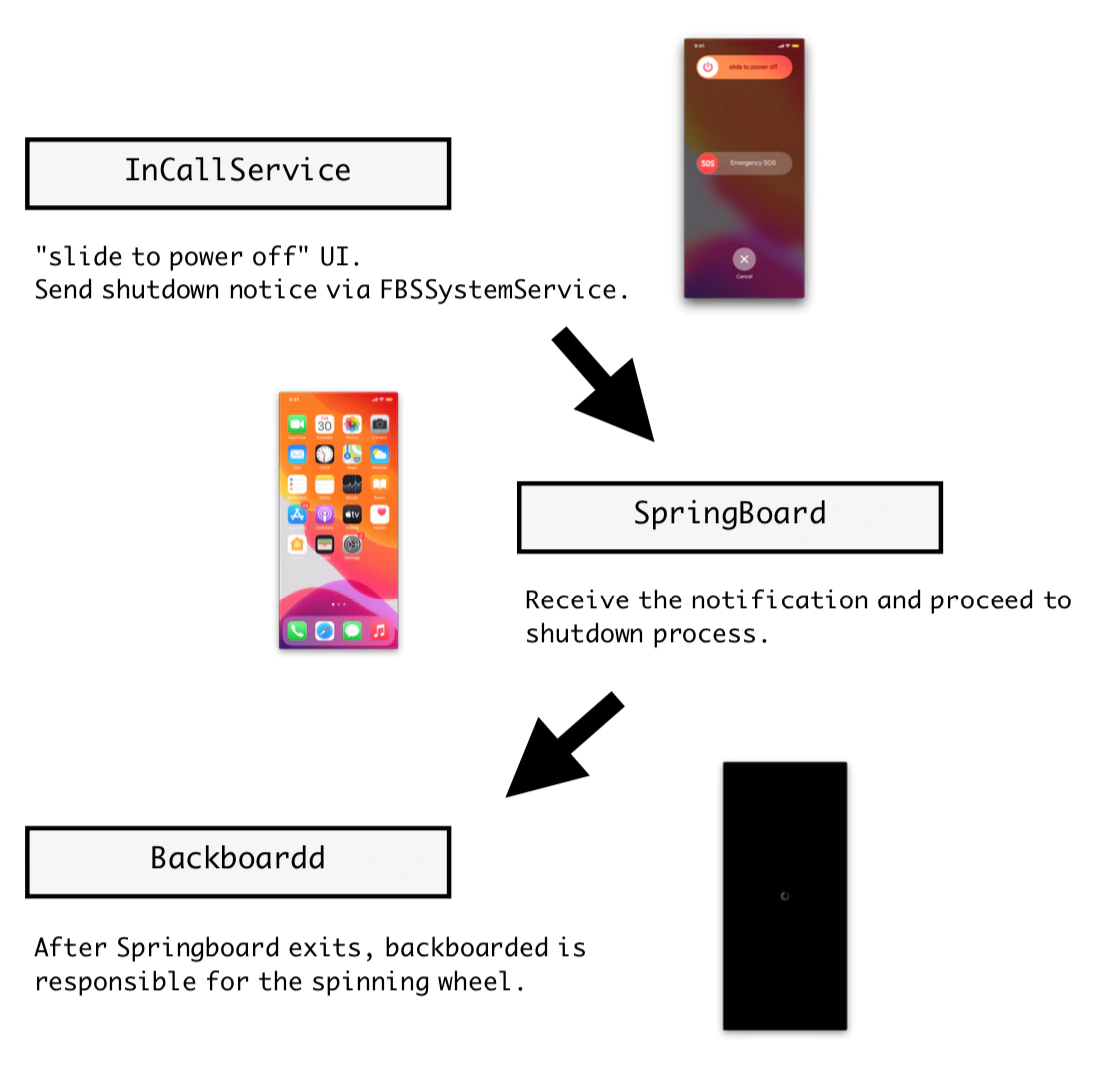
The bug can be exploited by injecting specially crafted code onto three iOS daemons, namely the InCallService, SpringBoard, and Backboardd.
The first thing it does, is calling the system app InCallService and force it to send a shutdown signal to SpringBoard, which refers to iOS's graphical user interface, and tell it to exit. Then, the malware tweaks the BackBoardd, the daemon that handles all touch and physical button click events, to display the Apple logo effect should the user opt to turn the running phone back on, while the malicious code continues to persist.
"We managed to hijack the signal by hooking the Objective-C method -[FBSSystemService shutdownWithOptions:]. Now instead of sending a shutdown signal to SpringBoard, it will notify both SpringBoard and backboardd to trigger the code we injected into them," the researchers said.
In other words, the codes imitate the process of shutting down an iOS/iPadOS device, by disabling all audio-visual cues associated with a powered-on device, including the screen, sounds, vibration, the camera indicator, and touch feedback.
"Despite that we disabled all physical feedback, the phone still remains fully functional and is capable of maintaining an active internet connection," the researchers explained.
Another say of saying it, the bug makes it possible to circumvent the normal practice of restarting a device to clear malicious activity from memory.
Making it even more persistent, any attempt of a force restart can be prevented because Backboardd monitors user input, including how long buttons are held.
The bug can prevent a forced restart by simulating the force restart just before a true restart takes place, such as by displaying the Apple logo early. This can fool victims into releasing the side button without genuinely triggering the real force restart.
"The user cannot feel a difference between a real shutdown and a "fake shutdown," the researchers said. "There is no user interface or any button feedback until the user turns the phone back 'on'."
At this time, there no evidence of a malware exploiting this bug in the wild. But if ever there is one that exists, malicious actors could make use of the bug to create a trojan that is highly persistent.
"The malicious actor could remotely manipulate the phone in a blatant way without worrying about being caught because the user is tricked into thinking that the phone is off, either being turned off by the victim or by malicious actors using 'low battery' as an excuse," the researchers said.
This finding suggests that bugs exist and it's only a matter of time before they are found. And in this case, even the iOS restart process isn't immune to being hijacked.
"Non-persistent threats achieved 'persistency' without persistence exploits." the researchers concluded.
The researchers have also made a proof-of-concept (PoC) to demonstrate this NoReboot.
