Just like most news publications on the internet, the news agency Fast Company uses Content Management System to manage the creation and modification of its digital content.
And this time, its website was hacked by a hacker, the outlet admitted.
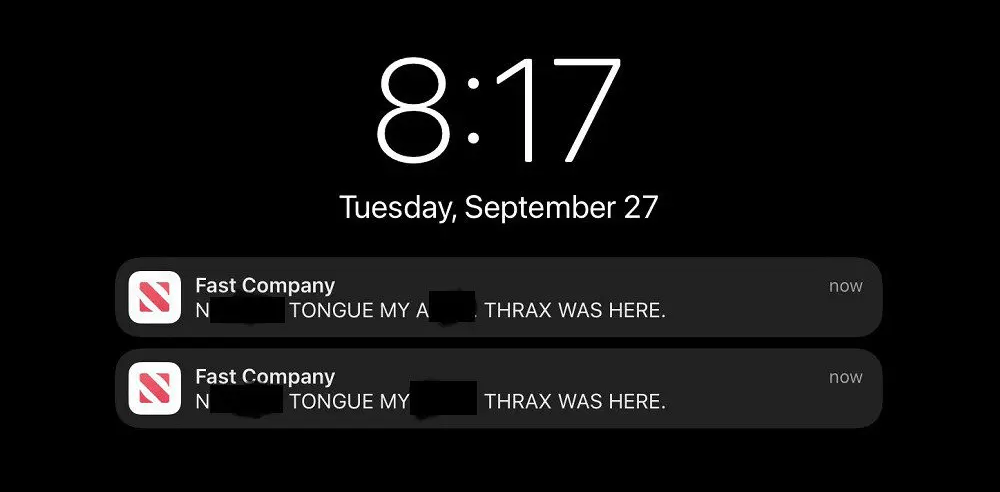
Following this breach, the hacker sent racist posts to Fast Company's Apple News account that "are vile and are not in line with the content and ethos of Fast Company."
To contain the breach and prevent further damage, Fast Company took an extraordinary step, which is to shut down its entire website.
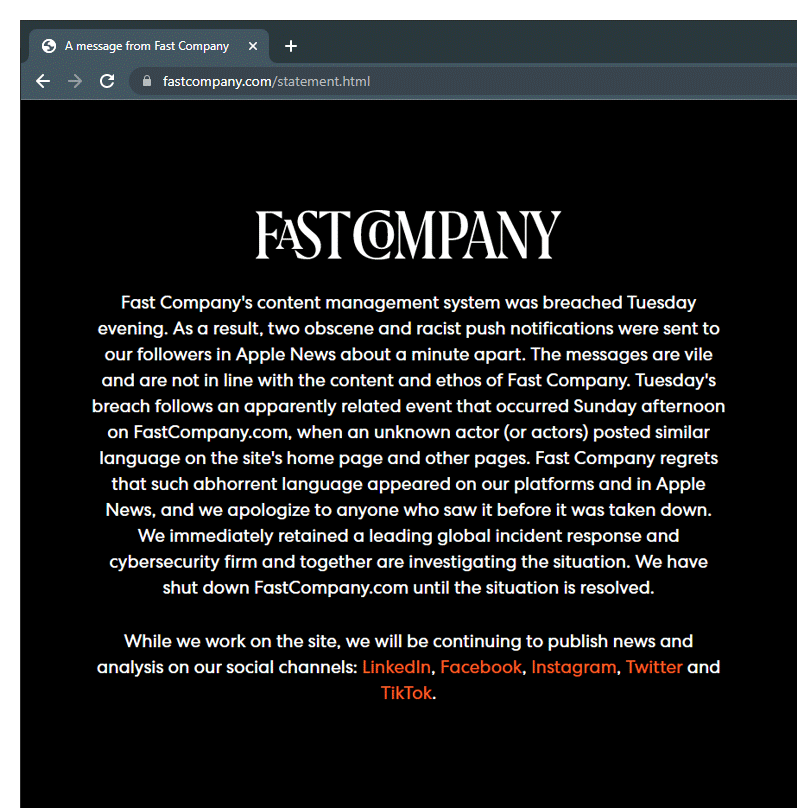
Initially, visiting Fast Company's website returned a 404 error. A few days later, the website was updated to show the following message:
"While we work on the site, we will be continuing to publish news and analysis on our social channels: LinkedIn, Facebook, Instagram, Twitter and TikTok."
To clarify: Fast Company’s content management system (CMS) was hacked on Tuesday evening, which impacted our Apple News alerts.
— Fast Company (@FastCompany) September 28, 2022
As for Apple, the tech titan also addressed the situation.
The company confirmed that Fast Company's website has been hacked and that it has suspended Fast Company’s Apple News account to help contain the damage.
It's worth noting that before Fast Company's website was taken offline, a hacker that goes by the name 'Thrax' claimed to be responsible for the breach.
The hacker posted an article labeled as sponsored content that detailed how they were able to infiltrate the publication.
The message claims that Fast Company had a “ridiculously easy” default password that was used across a number of accounts, including its administrator account.
Because of this, the alleged hacker had an easy access to the entire website, and was also able to steal a number of sensitive information, including authentication tokens, Apple News API keys, and Amazon Simple Email Service (SES) tokens.
This allowed the hacker to send emails using any @fastcompany.com email.
And not just that, because in a separate announcement, the alleged hacker wrote in a hacking forum, saying that they also managed to steal a database containing 6,737 Fast Company employee records.
The information within, include employees’ email addresses, password hashes for some of them, and unpublished drafts, among other information.
The hacker however, didn't have access to customer data, since it is stored in a separate database.
In a following news, it was realized that the hackers who took responsibility for the breach, said that they exploited an easily guessed default password, "pizza123."
The hackers managed to go deep into the business magazine's systems, simply because it reused that same and weak password across a dozen of its WordPress accounts, according to the hackers.
