Indonesia is a vast archipelago country in Southeast Asia, sitting on massive resources.
And this time, its National Data Center or Pusat Data Nasional (PDN) suffered a cyberattack by a hacking group, which "affected 210 institutions at the national and local levels," said Samuel Abrijani Pangerapan, the director general of informatics applications with the Communications and Informatics Ministry.
It didn't take long until the government restored many of the services, including the immigration services at airports and elsewhere are coming back to normal functionallity, after migrating many of them to Amazon Web Services (AWS).
But the efforts to recover other affected services, such as investment licensing, is proven difficult.
This is because the government says that it won't pay.

This decision is stressed by Communication and Informatics Minister Budi Arie Setiadi to journalists in an interview.
The Indonesian government took a firm stance by refusing to pay the ransom, emphasizing the importance of cybersecurity measures and data protection.
Because of this, efforts are on full throttle to restore all affected services.
It all began when the public first realized something was wrong, when government offices had to resource to manual works. Also, there were long queues at Soekarno-Hatta International Airport, the nation's main airport, resulting in long delays.
Then, it was realized by the government, that attackers held data hostage and offered a key for access in return for the $8 million ransom, said Herlan Wijanarko, the Director of Network and IT Solutions at Indonesia's state-owned communication company PT Telkom Indonesia.
Wijanarko said the company, in collaboration with authorities at home and abroad, is investigating and trying to break the encryption that made data inaccessible.
“We have tried our best to carry out recovery while the (National Cyber and Crypto Agency) is currently carrying out forensics,” Setiadi added.

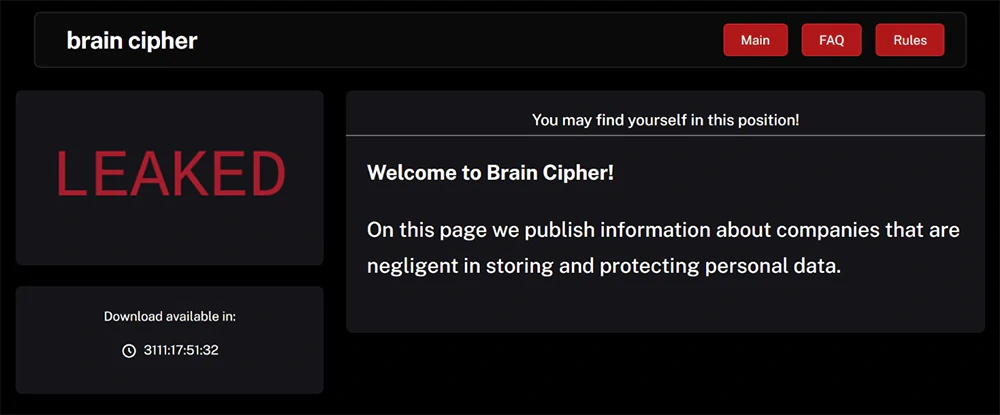
The ransomware that held the data as hostage, is said to be the Brain Cipher, which is a newer variant of the LockBit 3.0 ransomware.
The head of Telkom, Hinsa Siburian, said that the company detected samples of the ransomware, originally developed by Russian ransomware outfit LockBit.
The primary delivery method of LockBit is through phishing emails, often containing malicious attachments or links leading to malware downloads.
In this case, the Indonesian national PDN fell victim to Brain Cipher ransomware, when the strain managed to exfiltrates sensitive data and then encrypts it, following the double extortion model.
LockBit and its affiliates have targeted governments, major companies, schools and hospitals, causing billions of dollars of damage and extracting tens of millions in ransoms from victims.
The group was responsible for a quarter of all ransomware attacks worldwide in 2023, and has extorted over $1 billion from thousands of victims globally.
The top five countries hit by LockBit were the United States, Britain, France, Germany and China, according to Europol, the European Union's law enforcement agency.
And here, Indonesia fell victim, partly because it has a weak cyber security record, with poor online literacy and frequent leaks.
Pratama Persadha, Indonesia’s Cybersecurity Research Institute chairman, said the current cyberattack was the most severe in a series of ransomware attacks that have hit Indonesian government agencies and companies since 2017.
"The disruption to the national data center and days-long needed to recover the system means this ransomware attack was extraordinary," Persadha said.
"It shows that our cyber infrastructure and its server systems were not being handled well."
He said a ransomware attack would be meaningless if the government had a good backup that could automatically take over the main server of the national data center during a cyberattack.
Indonesia’s central bank was attacked by ransomware in 2022 but public services were not affected.
The health ministry’s COVID-19 app was hacked in 2021, exposing the personal data and health status of 1.3 million people.
Ransomware gang Brain Cipher announced they'll release decryption keys for free this Wednesday. They emphasized the need for cybersecurity funding and specialists. Apologies to Indonesia for the disruption. They request public acknowledgment of their decision. pic.twitter.com/FNNg0YsoAp
— Fusion Intelligence Center @ StealthMole (@stealthmole_int) July 1, 2024
Later, in a unique plot twist, the hackers behind Brain Cypher release key for disrupted data in ransomware attack, including the publication of the decryption key. The hackers provide this on a dedicated dark web website, alongside the steps to use it.
The move fulfills what they said earlier, in which they promised to release the data for free.
"We independently made such a decision," the group wrote on its site. "This did not require the intervention of special services and law enforcement agencies."
Brain Cipher added that it would permanently delete the data it stole during the attack once the government confirmed that the key was working and recovered the data. Otherwise, it threatened to disclose the locked data publicly if the government announced the recovery of the data on its own or with the help of any third party.
"Brain Cipher" Distributes Decryption Keys for Free
They released an additional statement on their dark web site with answers to seven popular questions. It includes reasons for attacking the data center and thanking the citizens of Indonesia for their patience, among other… pic.twitter.com/ngv1HH848i— Fusion Intelligence Center @ StealthMole (@stealthmole_int) July 3, 2024
Previously, while announcing its plan to release the key for free, the group also apologized for the ransomware attack, which disrupted various public services and affected the public.
Following the release of the key, Communications and Information Ministry applications and informatics director general Semuel Abrijani Pangerapan confirmed that they have obtained the key, and that the key is used successfully to unlock data.
"The technical team is still working on the rest of the databases," Semuel said.
