Virtual Private Network, or 'VPN', has become a term almost synonymous for internet security. There are a lot of things going on during a VPN connection, making the term complex to explain.
VPNs as a matter of fact, come in many different shapes. It can be overwhelming to distinguish them all and also between the technologies they use, let alone knowing what type of VPN is the best choice for your needs.
To make it simple, VPN can be divided into several categories: from environment and setup to protocols and features. However, term 'VPN' has become synonymous with 'VPN service'. For good reasons, there is a huge difference between VPN services and VPN technology.
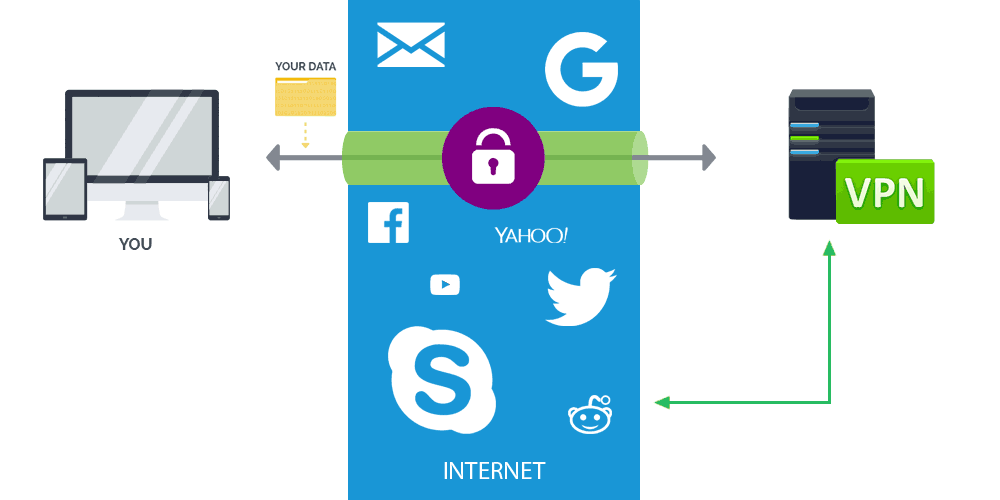
First of all, VPN by itself is the secure, private connection between your device and the endpoint - or your destination. In other words, think of your VPN service as your virtual toolbox that improves and reinforces your internet connection.
It utilizes a certain VPN protocol to encrypt and mask your internet traffic. This is where the VPN technology takes its role to keep your data safe.
By contrast, VPN services can be viewed as a package that may include several types of VPN technology, along with additional features and benefits.
Related: Staying Anonymous: Proxy, VPN Or Tor?
The Three Main Types of VPNs
VPNs can be divided into three main categories: Remote Access VPN, Intranet-Based Site-To-Site VPN, and Extranet-Based Site-To-Site VPN. Individual and normal users are most likely to encounter and use Remote Access VPNs, whereas big businesses often implement Site-To-Site VPNs for corporate purposes.
Remote Access VPN
For users of the web, either on desktop and mobile, the VPN service they use is most likely a Remote Access VPN. This type of VPN is the most popular.
Also called 'Virtual Private Dial-Up Networks (VPDNs), Remote Access VPNs connect users to a secure remote server in order to access a private network. The added encryption ensures that security isn’t compromised.
VPN services allow their users to use their own network when surfing the web. Using technologies, VPN services can hide users' traffic, mask and encrypt sent and received data, resulting in users' browsing experience secured and private.
Some VPN services offer users to change their location manually, allowing them to access contents of the web that are restricted to only certain locations.
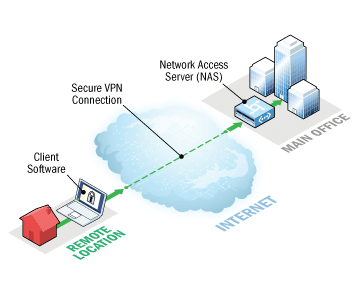
The main benefits of remote access VPNs are easy setups and hassle-free use. With the right software, this type of VPN can be easily accessible to newcomers and veterans alike, and is ideal for personal use. However, it may be unsuitable for (and even incompatible with) large-scale business needs.
There is also what is called a Host-To-Host VPN. This is very similar to Remote Access VPN, but with a small change. In a Host-To-Host VPN, two hosts are connected through a VPN tunnel, which is directly established between two hosts for a secured data transfer.
This type of VPN can be used when someone wants to connect to a specific network securely only, and isn't allowed to access other resources within that network.
Further reading: Using VPN At The Comfort Of Your Secured Home Internet. Yes Or No?
Site-To-Site VPN
If compared to Remote Access VPN, a Site-To-Site VPN is a totally different being.
While the former is more capable of personal usage, the later is designed to provide multiple users in various fixed locations with the ability to access each other’s resources.
There are two types of site-to-site VPNs: Intranet-Based Site-To-Site VPN and Extranet-Based Site-To-Site VPN.
Intranet-Based Site-To-Site VPN can be used by companies that have one or more remote locations. If employees wish to join in a single private network, the companies can create an Intranet-Based Site-To-Site VPN to connect each separate LAN to a single WAN.
In other words, Intranet-Based Site-To-Site VPN allows you to securely share the information and resources between each other.

And as for the Extranet-Based Site-To-Site VPN, it allows users to connect to two separate intranets, but without having the parties involved accessing the other directly. In this example, two companies working together can use this Extranet-Based Site-To-Site VPN service.
Site-To-Site VPNs are common in large-scale business environments where secure communication between departments is absolutely crucial. A Site-To-Site VPN requires large-scale encryption and dedicated equipment.
With more customization and requirements, Site-Site VPNs are less flexible than Remote Access VPNs.
Types Of VPN Protocols
The next things to know, is the technologies (protocols) behind VPN services.
Internet Protocol Security (IPSec)
Internet Protocol Security, also known as IPSec, is used to secure internet communication across an IP network. IPSec secures all IP communication by verifying users' session and encrypts each data packet during the connection.
IPSec runs in 2 different modes:
- Transport Mode to encrypt the message in the data packet.
- Tunneling Mode to encrypt the whole data packet.
IPSec can also be used with other security protocols to improve the security system.
Layer 2 Tunneling Protocol (L2TP)
L2TP or Layer 2 Tunneling Protocol is the tunneling protocol often combined with another VPN security protocol like IPSec to establish a a secure VPN connection. L2TP creates a tunnel between two L2TP connection points, whereas the IPSec Protocol encrypts the data and maintains secure communication between the tunnel.
Point-To-Point Tunneling Protocol (PPTP)
PPTP or Point-to-Point Tunneling Protocol creates a tunnel and confines the data packet inside it. Point-To-Point Protocol (PPP) is used to encrypt the data between the connection. PPTP is one of the most widely used VPN protocol and has been in use since the early release of Microsoft Windows.
PPTP is also used on Mac and Linux.
SSL And TLS
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) generate a VPN connection where users' web browser acts as the client. Here, user access is prohibited to specific applications instead of the entire network.
E-commerce sites commonly use both SSL and TLS protocol. For end users, it's easy to switch to between the protocols from their web browsers since there is almost no action required. This is because modern web browsers are equipped with SSL and TLS.
SSL connections have 'HTTPS' instead of 'HTTP'.
OpenVPN
OpenVPN is an open-source VPN software that implements VPN techniques to create secure Point-To-Point and Site-To-Site connections in routed or bridged configurations and remote access facilities. It uses a traditional custom security protocol based on SSL and TLS protocol for key exchange
Secure Shell (SSH)
Secure Shell, or simply SSH, generates the VPN tunnel through which the data transfer happens. It also ensures that the tunnel is encrypted. SSH connections are generated by a SSH client and data is transferred from a local port on to the remote server through the encrypted tunnel.
Bottom Line

Whatever VPN you choose, you may only be able to use one type of VPN technology at a time. However in most cases, you can have the choice to switch between them via your VPN service. The best VPN providers support a great deal of protocols and features, allowing you to pick the most suitable type of service depending on your needs and requirements.
For most users of the web who simply want to avoid government's surveillance or their local ISP's control, they can use Remote Access VPN. This kind of VPN offers sufficient protection and flexibility for daily usage.
The service can come for free or for purchase, but what's important is that, the VPN should not leak your real IP address, nor log your session.
For corporate users, Site-To-Site VPNs have a lot of benefits. The Intranet-Based Site-To-Site VPN for example, can be the best choice for users working in remote offices. And as for the Extranet-Based Site-To-Site VPN, can be the solution for users who want to connect with others in a different company.
There are many different types of VPNs, and a lot of services to choose from. For what matters, you need to choose the right one based on your budget, and required functionality.
In other words, your choice depends heavily on your needs and expectations.
