Android is a very capable operating system. It's very popular and powerful, and it's extremely customizable.
But with those advantages come a list of disadvantages. And the most prominent, is its endless stream of malware-ridden apps found lurking on Google Play Store, the official app store for Android devices.
And this time, a number of apps have been found infecting more than 300,000 users with a trojan capable of stealing banking information.
As reported by ThreatFabric, the cybersecurity firm only disclosed a few of the malicious apps, but they include QR scanners, PDF scanners, fitness trackers, and cryptocurrency apps.
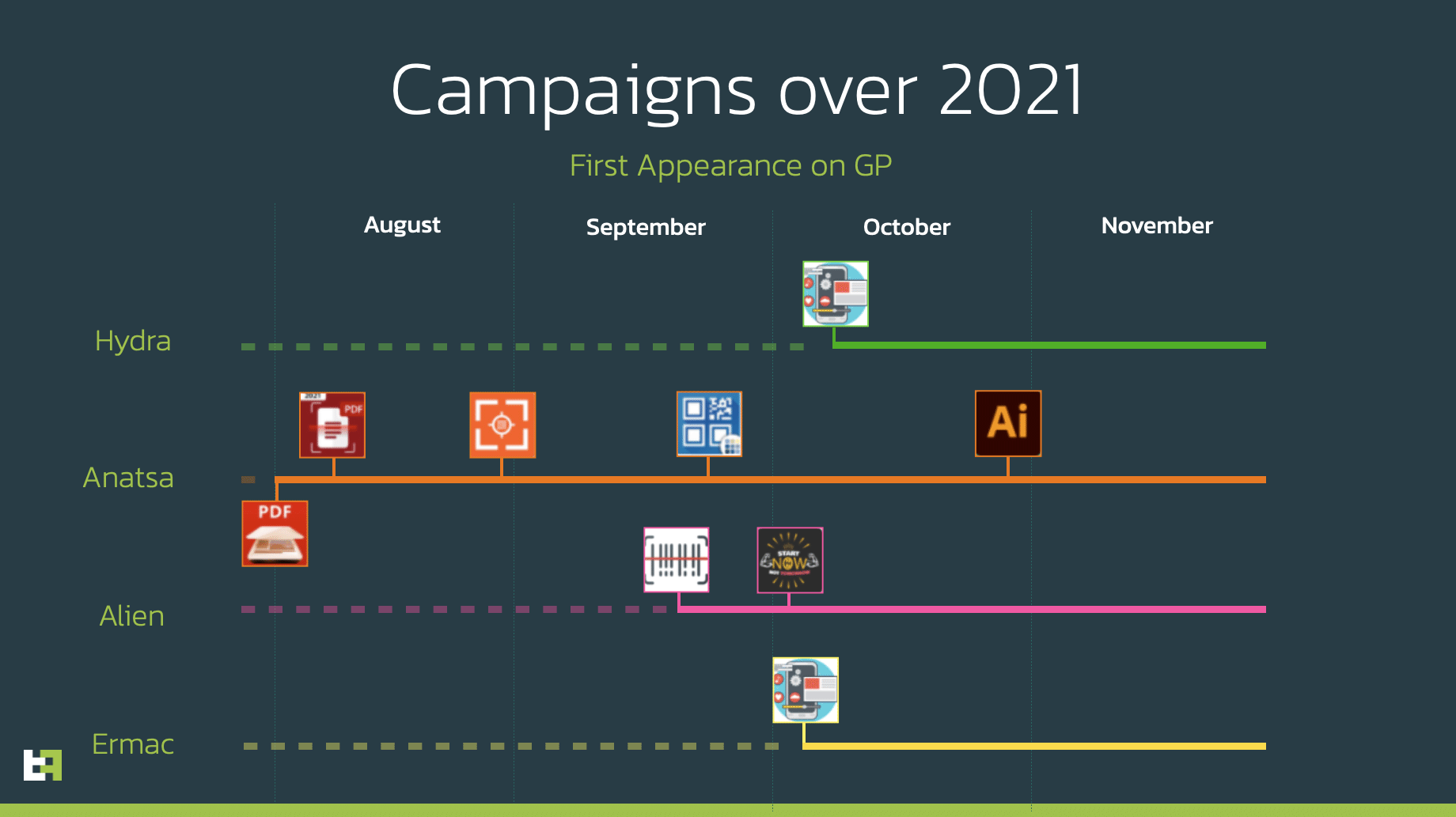
The researchers classified the malware used by the apps into four different families:
- Anatsa: The largest of the four malware families, with more than 200,000 combined downloads. The trojan uses Android’s screen capture to steal login information and other personal data.
- Alien: The second-most downloaded trojan that was found on over 95,000 devices. Alien intercepts two-factor authentication (2FA) codes.
- Hydra and ERMAC: The last two families that racked up a combined 15,000 downloads, can remotely access a user’s device and steal banking information.
Read: ERMAC, The Malware Capable Of Stealing From Hundreds Of Banking And Wallet Apps
The apps that were found using the above four malware families have been distributed on Google Play Store for over four months before the researchers at ThreatFabric found them.
Fortunately, the apps have been removed by Google.
Google was also able to deactivate the apps on any devices they were installed on.
The real issue however, is how hackers managed to sneak the malware into the apps in the first place.
Normally, Google can catch and remove apps with suspicious code automatically, sometimes without having to have humans doing all the work.
However, these malicious apps didn't have malware when they were still in the Play Store.
No malware, and no virus.
"What makes these Google Play distribution campaigns very difficult to detect from an automation (sandbox) and machine learning perspective is that dropper apps all have a very small malicious footprint," wrote the researchers from ThreatFabric in a blog post.
"This small footprint is a (direct) consequence of the permission restrictions enforced by Google Play."
The apps managed to bypass Google's all-seeing eye, by not having the malware at all.
The apps also work as intended, just like advertised. This prevented victims from becoming suspicious, and may even keep using them.
This is where the bad actors made their sneaky attack.
After a period of time, the apps will instruct users to download further updates, promising them a better experience and even more features.
The thing is, the required updates had to be downloaded from third-party sources. But by then, many users had come to trust them because things just work.
Unlike most other fake apps that falsely advertise their features, many of the apps in this batch of malicious Android software worked as intended. But behind the scenes, the apps were stealing passwords and other user data.
Using this method, the malicious developers can submit their apps without tripping Google’s detection.
But just like most other cases before this, the malware-infested apps do show some signs that only those with keen senses will notice: the apps will begin asking more permissions than necessary. The apps can even ask for Accessibility Services privileges or forced users to sideload additional software.
