
Typos are extremely common. No matter how used people are with typing with keyboards, misspelling does happen.
To make things convenient, two popular web browsers, Google Chrome and Microsoft Edge, have spell checkers. The feature is meant to help those who mistype words when typing documents through the browsers, or when browsing the web, creating social media posts, and more.
Google Chrome users could enable the spell check feature by enabling what's called the enhanced spell check in Chrome’s settings. For users on Microsoft Edge, they can add the browser extension Microsoft Editor Spelling & Grammar Checker to the browser to use the spell checker.
The thing is, these two spell checkers can work beyond what they're supposed to.
This is because the spell checkers are designed and purposefully developed to scan for typos, and correct them. And to make this work, the two companies' spell checkers must be able to read what users type.
And to correct them, both browsers' spell checkers need to contact their servers.
What this means, the data users input in forms will be transmitted back to either company.
Depending on what websites users visit, data that either Google or Microsoft can see, can include Social Security number, name, address, email, date of birth, contact information, bank and payment information or other sensitive personal data.
In short, Google Chrome and Microsoft Edge can essentially send users' personally identifiable information (PII) to either company.
It was the co-founder and CTO of the JavaScript security firm otto-js, Josh Summit, who discovered it first.
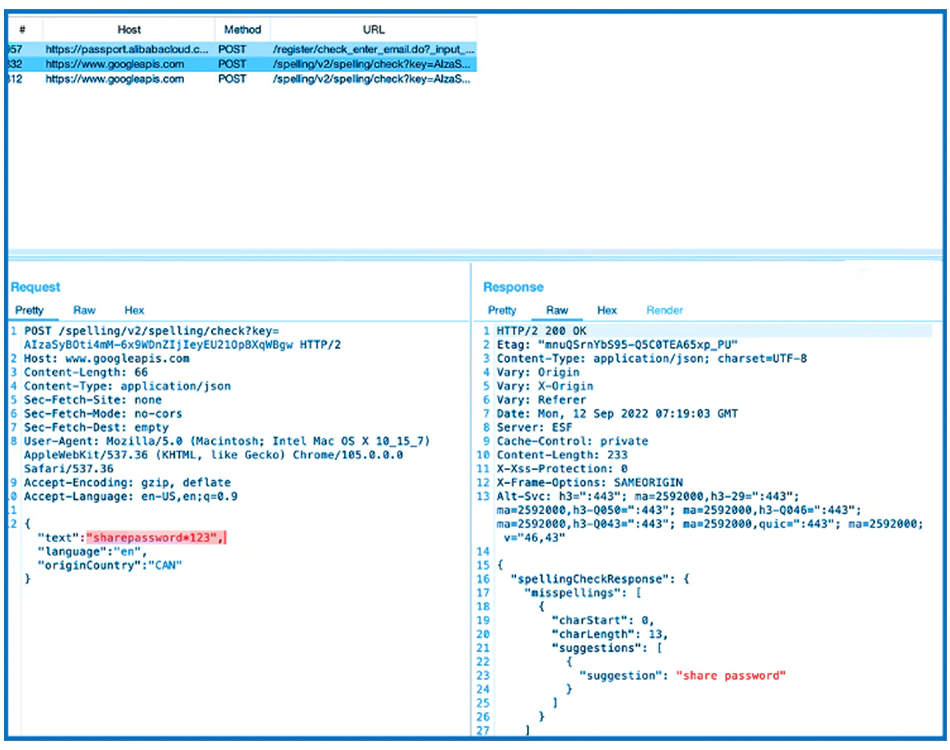
In a report, he said that he found that personal information as well as passwords are sent back to Google and Microsoft, when using Enhanced spell check or Microsoft Editor.
Summit discovered this when he and his team was testing his company’s JavaScript script behavior detection.
He said that "basically anything" entered into a site’s form fields is sent to either Google or Microsoft when using Chrome or Edge with this feature enabled.
Making things even worse, the feature can also send back users' passwords.
Both Chrome and Edge hide anything within the password field with asterisks.
This is done for security purposes.
Asterisks are displayed to represent the characters that users inputted. Each asterisk represents one character, and this is mean to indicate that a character of a password or other confidential information has been entered, without the risk of displaying the actual character.
The thing is, people hate typos so much, that many platforms provide their users the ability to "show password."
For convenience, this allows users to see the password they entered, to ensure that it is right, before submitting.
The thing is, the two browsers' spell checkers can also sends passwords when they are showed, back to their servers.
Chrome and Edge are literally "spell-Jacking your data," Summit said.
"If 'show password' is enabled, the feature even sends your password to their 3rd-party servers. While researching for data leaks in different browsers, we found a combination of features that, once enabled, will unnecessarily expose sensitive data to 3rd Parties like Google and Microsoft. What's concerning is how easy these features are to enable and that most users will enable these features without really realizing what is happening in the background," he said.
Users of the browsers should be worry.
To maintain privacy and preventing from having sensitive data falling to the wrong hands, they may as well check to see whether or not the feature is enabled, and turn it off if its on.
When asked by Bleeping Computer, Google explained that its enhanced spell check is only enabled on an opt-in basis, and before the feature can be turned on, users are warned that turning it on means that all their input data is sent off to its servers.
The company then went on to make clear that it is aware that the data may sometimes be sensitive.
This is why Chrome's spell checker doesn't attach any text users input to any users identity.
The company also said that data it receives from the spell checker is stored only for processing the spell checking, and after that, it will be removed.
The company further vowed to improve its own processes to exclude passwords from being processed proactively.
