
When one software looks and feels the same as the other, there is one thing that can differentiate them.
Software is just a bunch of codes put together. But not all software have the same privileges and levels of access. On Android, the operating system assigns different levels of permissions using unique user IDs (UIDs). And everything is built on certificates that are given out by app developers and device manufacturers.
This helps Android prove that an app version is legitimate.
Catastrophe can happen when these certificates leaked out.
When this happens, bad actors can sign their malware with the leaked certificate, in order to make their malware look like legitimate system apps.
This is what exactly happened to a number of vendors’ platform certificates, which have been found in circulation and actively used by bad actors.
New APVI entry: platform certificates used to sign malware
Found by yours truly :)https://t.co/qiFMJW111A— Łukasz (@[email protected]) (@maldr0id) November 30, 2022
The leak was first spotted by Google malware reverse engineering expert Łukasz Siewierski.
He found that the certificates in question are platform certificates meant to verify the authenticity of the “android” application that’s part of every phone, but are also used to sign individual apps from manufacturers.
The biggest issue here is that, the leaked certificates are part of Android's core application, which have the ability to grant the highest level of access to the system.
What this means, the certificates are meant to allow an almost unrestricted access to user data.
Without this certificate access, Android malware has to ask for permissions in order to gain deeper access to its victims' devices. For example, a malware may ask victims' access to accessibility services, which it then uses to extract data and information from other apps.
But when the same malware is signed using a "trusted" certificate that is the same as the one used by root android applications, it doesn’t need to ask permissions.
Bad actors who develop their malware and signed it with the leaked certificate, could have their malware gain elevated system access without any user interaction.
Making things worse, the malware could also pretend to be a trusted pre-installed app and appear as an update to users, making it even harder to spot that something is wrong.
As disclosed in Google’s Android Partner Vulnerability Initiative, a handful of platform certificates have leaked out, including the ones from Samsung, LG, Xiaomi, Mediatek, and more smaller vendors.
While smaller vendors may not pose huge damage considering the number of users they have, but bigger vendors, like Samsung, can certainly cause issues.
The South Korean conglomerate company uses the leaked signature to sign hundreds of its apps. And pair that with the fact that Samsung is the single biggest Android manufacturer out there, the damage can be huge.
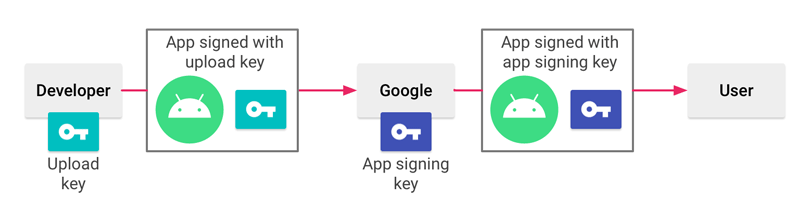
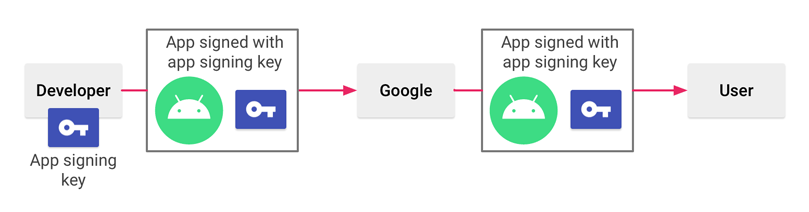
Google as the commercial entity behind Android, knows how sensitive certificates can be, and has recommended manufacturers to limit their usage.
Fortunately, affected Android manufacturers have been notified, and have started fixing the issue.
While leaked certificates can cause a whole lot of damage, security on the Play Store itself isn’t paramount, Android users are still urged to only download apps from legitimate app stores, and refrain from downloading anything from unknown sources, or sideloading apps.
Even though malware-ridden apps do get into the Google Play Store, the official Android app store is still safest source for downloading Android apps.
