Malware is a software, nothing more and nothing less. But this can make them very dangerous.
With the internet, people are sending and receiving information from anywhere, and at anytime. Data is abundance, and in between those massive amount of information, malware thrives by jumping from one inbox to the next, from one attachment to another.
And here, analysts have reportedly discovered the source of the sextortion emails that have plagued the internet since at least 2018.
The sextortion emails were sent to millions of people around the world, forcing people to send the bad actors a sum of money in the form of Bitcoin, or instead have their intimate moments shared on the internet.
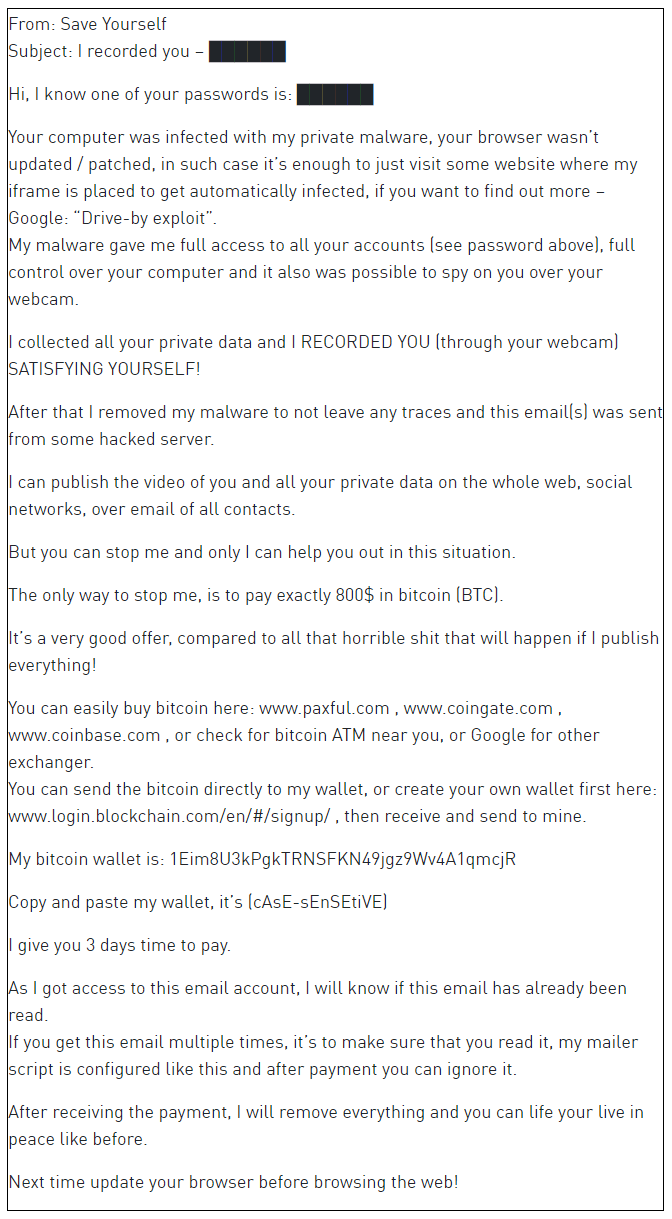
Reason Cybersecurity researchers dubbed this malware 'Save Yourself', and it does more than what it seems.
It started back on the days of 'Phorpiex' (aka Trik) botnet. First documented in 2016, the botnet has been exploited by multiple threat actors to distribute malicious payloads.
The malware that has been active for at least a decade, operates more than 500,000 infected hosts. In the past, attackers using Phorpiex monetize their malicious deeds by distributing other malware, including GandCrab, Pony, Pushdo, and used its hosts to mine cryptocurrency.
But Phorpiex evolved, and added another form of revenue generation: sextortion campaigns.
And 'Save Yourself' is the name of this campaign.
The name comes from the sextortion email people receive, from senders like [email protected]. With the emails, the bad actors state that a dangerous malware has infected the recipient's machine, but according to Reason Cybersecurity, it goes more than just that.
The firm found that the malware can also force devices to act as blackmail proxies, which are capable of mining privacy-focused cryptocurrency Monero.
"Check Point Research monitored the campaign and the Bitcoin wallets extracted from every spam bot spotted since April 2019. We found that more than 14 BTC were transferred to those wallets:," said Check Point researchers in its website post.
But before any of that can happen, the Phorpiex/Trik botnet used a spam bot to download a database of email addresses from a C&C server. After that, an email address is then randomly selected from the downloaded database, with a message automatically composed from the several hardcoded strings.
To make the sextortion campaign more persuasive, the Save Yourself emails can contain the recipients' password, which apparently have been gathered from databases of leaked credentials, like Have I been Pwned?, said Check Point researcher Alexey Bukhteyev.
"Leaked credential lists, containing passwords that are often not compatible with their linked email addresses, are a common inexpensive commodity," the researchers concluded. "Phorpiex, a veteran botnet, has found a way to use them to generate a low maintenance, easy income on a long term basis."
This spam bot can generate up to 30,000 spam emails per hour, with each individual spam campaign can affect up to 27 million potential victims.
In other words, Save Yourself is a well-established malware and botnet agent.
With it spreading like wildfire through people's inboxes, the developers behind Save Yourself are looking for a large-scale sextortion campaign and cryptojacking that target innocent recipients.
However, it should be noted that the initial sextortion emails don't actually mean real infection. People can only fall as victims when they inadvertently download or click on links sent or intended by the attackers.
But when that happens, hell breaks loose. The malware can do whatever it wants.

The first and utmost, is mining cryptocurrency without the victim's knowledge. Save Yourself can avoid detection because it only uses 50 percent of the infected machine’s CPU to mine Monero. This way, the victim won't experience noticeable slow down and won't be suspicious.
The malware can also reportedly read clipboard data and replace Bitcoin wallet addresses with its own, presumably to redirect cryptocurrency transactions to the attackers.
Save Yourself can also compromise executable files found on the target machine to ensure automatic infection any time the user runs such files.
"The desired executable will then run as it should, so the user won’t suspect that there’s anything wrong,” said Reason. “Nor will anything look suspicious when analyzing the sample since – at first glance, it will look like known software (icon, signature, strings, functionality)."
Save Yourself can go beyond that, as it can also steal information, steal credentials, and can even plant more malware.
It is very possible that the malware author has gathered and combined several viruses and modified them to suit their own needs,” explained Reason on its blog post.
According to Bukhteyev, 25% of victims are located in India.
Major email providers can automatically protecting users against the sextortion emails. However, the attackers are pivoting, as they started demanding Litecoin instead of Bitcoin to dodge those email filters.
Fortunately, the firm noted that most antivirus solutions should detect and clear the malware.
Related: Researchers Found 'Varenyky', A French Malware That Does More Than Just Sextortion