
Security researchers have issued a chilling warning about dozens of the most popular VPN apps available on Google Play.
A sweeping, peer-reviewed study has uncovered that more than 20 of these apps, together downloaded over 700 million times, are not what they claim to be. Instead of being independent services, they belong to just three hidden "families" of VPN providers, quietly tied to companies in China and Russia, and all sharing the same infrastructures, codebases, and most dangerously, the same security flaws.
The investigation, called "Hidden Links: Analyzing Secret Families of VPN Apps" (PDF), was conducted by The Citizen Lab at the University of Toronto in collaboration with Arizona State University, and published in the Privacy Enhancing Technologies Symposium (PETS) journal.
By digging into business records, APK code, and technical infrastructure, the researchers discovered deep connections between apps that present themselves as competing services.
But in the back, the researchers found that the companies deploy both deceptive marketing and serious risks to user security.
Read: Choosing The Best VPN: Know How To Protect Yourself
At first glance, these VPNs appear to be a diverse selection of services on the Play Store.
Each and everyone of them has unique branding, flashy logos, and different developer names. To the average user, they look legit and can be trusted. It looks like they're just products competing in a healthy competition.
But the research shows otherwise.
In reality, many of these VPNs are run by the same small circle of providers.
What this literally means, when users think they’re switching to a new provider for better privacy or security after dumping a product, they may just be picking another skin of the same flawed system.
Researchers called this not only a breach of trust, but a way to give consumers a false sense of choice in an industry where transparency is supposed to be paramount.
The study grouped the apps into three distinct families, each with shared infrastructure and identical or near-identical codebases.
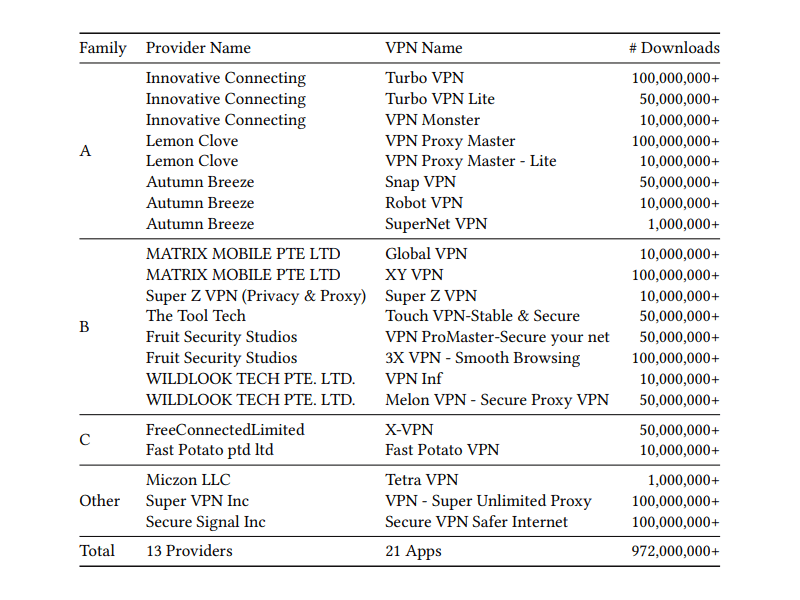
- Family A: Turbo VPN, Turbo VPN Lite, VPN Monster, VPN Proxy Master, VPN Proxy Master Lite, Snap VPN, Robot VPN, SuperNet VPN.
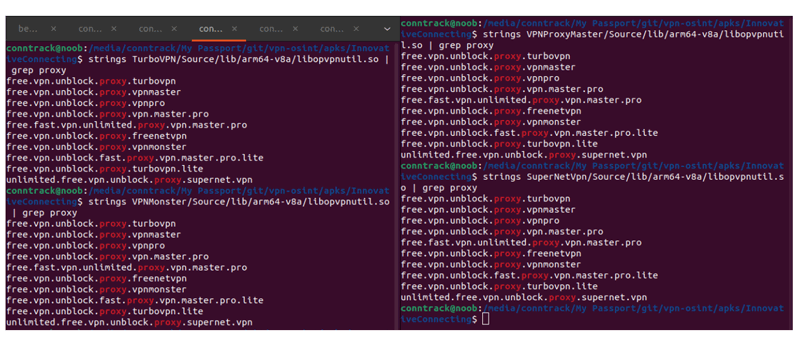
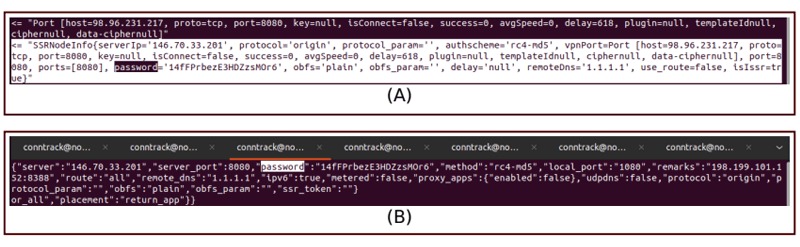
The operators behind them include: Innovative Connecting, Autumn Breeze, and Lemon Clove. All of these three providers have been tied to Qihoo 360, a major Chinese cybersecurity firm sanctioned by the U.S. for connections to the People’s Liberation Army. The researchers found that the apps reused the same encryption methods, carried identical assets, and all contained a hard-coded password for Shadowsocks, a proxy tool.
- Family B: Global VPN, XY VPN, Super Z VPN, Touch VPN (Stable & Secure), VPN ProMaster (including Lite and Secure Your Net variants), 3X VPN – Smooth Browsing, VPN Inf, Melon VPN.
Operators include a cluster of providers including Matrix Mobile, ForeRaya Technology, and Wildlook Tech. These apps are found to have been using the same VPN server addresses and were found to secretly collect IP-based location data despite privacy policies claiming otherwise. They too relied on Shadowsocks with insecure hard-coded credentials.
- Family C: X-VPN, Fast Potato VPN, Tetra VPN.
Operators behind them include: Free Connected Limited and Fast Potato. These apps were built on nearly identical custom VPN protocols, shared infrastructure, and repeated the same outdated encryption and blind on-path attack vulnerabilities.
The study uncovered several serious weaknesses common across these families.
From reusing and hard-coding Shadowsocks keys means that network eavesdropper sitting between the VPN client and server can decrypt all communications for every user of the affected apps. They also use deprecated encryption algorithms instead of robust, modern ciphers. Then, there is the fact that the apps are vulnerable to attacks where a hacker on the same network (e.g., public Wi-Fi) can intercept and manipulate traffic without detection.
The researchers also found that the companies don't share how they gather or use user data.
Despite having their own respective privacy policies, researchers found the apps requested location data from services and uploaded it to remote databases, raising suspicions of hidden data harvesting.
"Google is potentially exposing its brand to reputational damage by hosting and profiting from deceptive and insecure apps like the ones we investigated," the researchers said.
This is however, is inevitable, and that it has always been the bigger problem with using free VPN services.
VPNs are marketed as tools for privacy, anonymity, and bypassing restrictions. People rely on them to access censored content, secure themselves on public Wi-Fi, and even to avoid surveillance. But to provide these services, the companies behind them require computing power, and expenses that necessary for their longevity.
As a result, some may not focus on providing the services they promise, but cut costs, and also earn money elsewhere, like selling user data.
And this research proves that not all VPNs are created equal, and that not all of them are built to protect users.

The researchers suggest that the many "free" VPNs may be designed for the opposite of what they say they are. Instead of protecting user data, they are purposefully built to collect data under the guise of protecting it.
If a VPN provider is dishonest about its ownership and careless with its infrastructure, users can’t trust that their browsing, personal data, or communications are truly safe.
As the Citizen Lab researchers put it, these apps appear to be “designed to do something other than keep you safe online.”
Experts recommend users of the aforementioned VPN apps to delete the apps and switch to a trusted provider that has been independently audited, provides transparent ownership, and has a a reputation for strong encryption practices.
This research should be a wake-up call for anyone who assumes that downloading a top-ranked app from the Play Store guarantees safety. The “Hidden Links” study shows that even the most popular VPNs can be insecure, deceptive, and potentially dangerous.
