Bluetooth is not a new technology nor it is the safest of them all.
But still, it has been on the facets of many people's daily lives. People use Bluetooth for everything from connecting their earphones to their phones, to connecting peripherals to their computers or sending files to other devices. Bluetooth is reliable in its own term, and people simply love it.
However, this time and again, a bug on the technology has been found.
According to researchers at the University of California San Diego, a security and privacy issue is found on the way Bluetooth Low Energy (BLE) is communicating.
Rather than breaking the encryption of the data within the signal, the researchers found the flaw after identifying the unique features of radio signals being broadcast.
On their research paper (PDF):
for COVID-19, and even finding lost devices.
These applications use cryptographic anonymity that limit an adversary’s ability to use these beacons to stalk a user.
However, attackers can bypass these defenses by fingerprinting the unique physical-layer imperfections in the transmissions of specific devices.
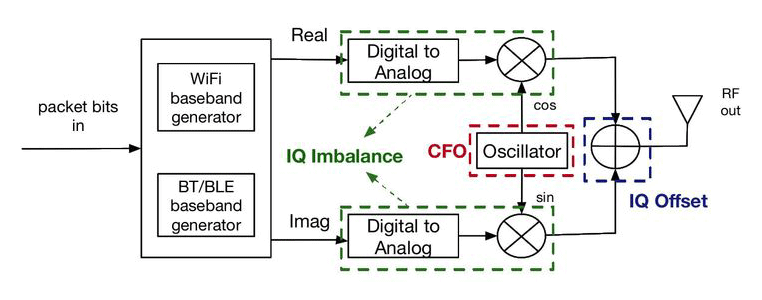
The researchers found that all wireless transmitters have signal variance.
And this variance can be unique to each phone.
The researchers then isolated the signal from the underlying data, and realized that BLE has a unique marker for the broadcasting service.
In other words, BLE emits signal that contains the fingerprint data of the device it is emitted from.
The researchers tested this with a Google Pixel 5 phone, and found that the signal it emitted had a false negative rate of 0%.
What this means, the researchers who isolated the signal from the data, managed to correctly identify the phone among radio signals, a 100% of the time.
The researchers managed to flawlessly fingerprint devices that communicate with BLE.
BLE is designed to reduce the power consumption of traditional Bluetooth at the cost of a bit of bandwidth and range.
Using the low power capability, BLE can work by consuming about 1% of the energy needed to power traditional Bluetooth.
Due to this advantage, BLE-equipped devices can be kept on to broadcast its signal constantly.
It should be noted that not all imperfections in this BLE issue are unique.
Some BLE chipsets produce similar imperfections making them harder to uniquely identify. Furthermore, this method of fingerprinting can also be affected by temperature, making hacks difficult in environments outside lab conditions.
The researchers suggest that simple software update won't be able to fix this issue. Instead, the researchers said that "adding a random time-varying extra frequency" can offset the receiver, and can make the signal unpredictable.
