Cryptocurrency is still the hype. While prices fluctuate, there are a lot of people who want to own cryptocurrencies. And some of them are going to great length to obtain them.
This time, hackers are hacking thousands of high-profile YouTube accounts in order to hijack their channels.
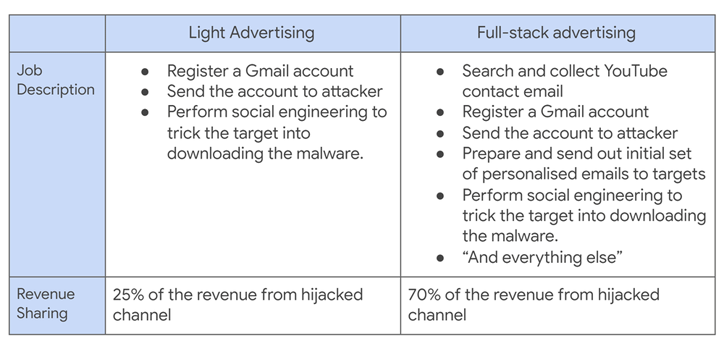
Coordinated by financially-motivated threat actors, the campaign was first spotted back in 2019 by Google's Threat Analysis Group. The researchers found that multiple hack-for-hire individuals were recruited through job ads on Russian-speaking forums.
This campaign uses password-stealing malware that is distributed through phishing attacks, done using social engineering to create customize emails based on each YouTuber.
Once delivered and installed on the targets' systems, the malware can steal login credentials as well as browser cookies.
It's through these, that allowed the hackers to hijack victims' accounts.
According to Ashley Shen, a TAG Security Engineer, in a blog post:
"Most of the observed malware was capable of stealing both user passwords and cookies. Some of the samples employed several anti-sandboxing techniques including enlarged files, encrypted archive and download IP cloaking."
The attack exploits how YouTube creators often place their contact email address in their channel's about page to solicit advertising deals.
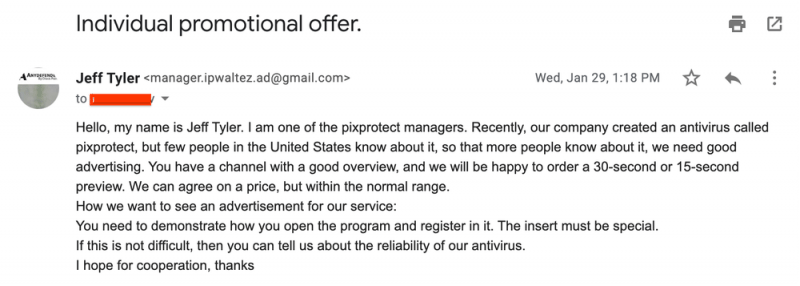
After collecting the email addresses, the hackers create phishing emails by impersonating an existing company. For example, the hackers will create inquiries about advertising opportunities to promote a product such as a VPN, antivirus software, a music player, an online game, or a photo-editing app.
The hackers will then ask the YouTube creator to try out the product, while in reality, the product is to trick the content creator into installing a malware onto their computer.
The malware being used include strains like RedLine, Vidar, Predator The Thief, Nexus stealer, Azorult, Raccoon, Grand Stealer, Vikro Stealer, Masad, and Kantal, and open-source ones like Sorano and AdamantiumThief.
"Once the target agreed to the deal, a malware landing page disguised as a software download URL was sent via email or a PDF on Google Drive, and in a few cases, Google documents containing the phishing links," the company said.
When victims fell for the trick, they infect their computers with malware. And this malware is giving hackers the access to their computers.
Google identified roughly 15,000 user accounts and 1,000 internet domains to impersonate various companies, such as Cisco, photo-editing company Luminar, and game developers on Steam, specifically created for this campaign
"During the pandemic, we also uncovered attackers posing as news providers with a ‘Covid19 news software,’" said Google.
When the hackers managed to log in to their victims' accounts on their behalf, the hackers can then hijack the victims' YouTube accounts, to then rebranded the channels in order to impersonate high-profile tech executives or cryptocurrency exchange firms.
"The channel name, profile picture and content were all replaced with cryptocurrency branding to impersonate large tech or cryptocurrency exchange firms," explained Google.
Through these, the hackers can stream live cryptocurrency scams, which entice viewers to send Bitcoin to a digital wallet with the promise of a larger payout. In reality, viewers will get nothing.
Other YouTube accounts that aren't used, or have been used up, are then sold to underground account-trading markets.
The hackers sell the stolen accounts for anything between $3 to $4,000, depending on their total number of subscribers.
In response to this campaign, Google's Threat Analysis Group cut down phishing emails linked to these attacks on Gmail by 99.6% since May 2021.
"We blocked 1.6M messages to targets, displayed ~62K Safe Browsing phishing page warnings, blocked 2.4K files, and successfully restored ~4K accounts," Shen said. "With increased detection efforts, we've observed attackers shifting away from Gmail to other email providers (mostly email.cz, seznam.cz, post.cz and aol.com)."
Google also reported this malicious activity to the FBI for further investigation to protect YouTube users and creators targeted in the campaign.