Russia-linked hackers have hacked the software provider Kaseya, a Miami-based information technology company that provides IT services to small and medium-sized businesses.
After the hack, the group better known as REvil, has its operations suddenly terminated. The group's public representative suddenly went quiet.
But shortly after that, only months later, REvil operators restarted their operations. Their websites returned online, and things seemed to go back to normal.
However, the gang's ransomware operations were struggling to recruit personnel. The group even went as far as increasing its affiliate's commissions to 90% to entice other threat actors to work with the group.
Amid the internal issues, the hacker gang's websites were then hacked.
An unknown individual managed to hijack the group's Tor payment portal and data leak blog.
Read: Kaseya Hackers Demand $70 Million Following Their Massive Ransomware Attack
As a result, the Tor sites operated by REvil had to be taken offline.
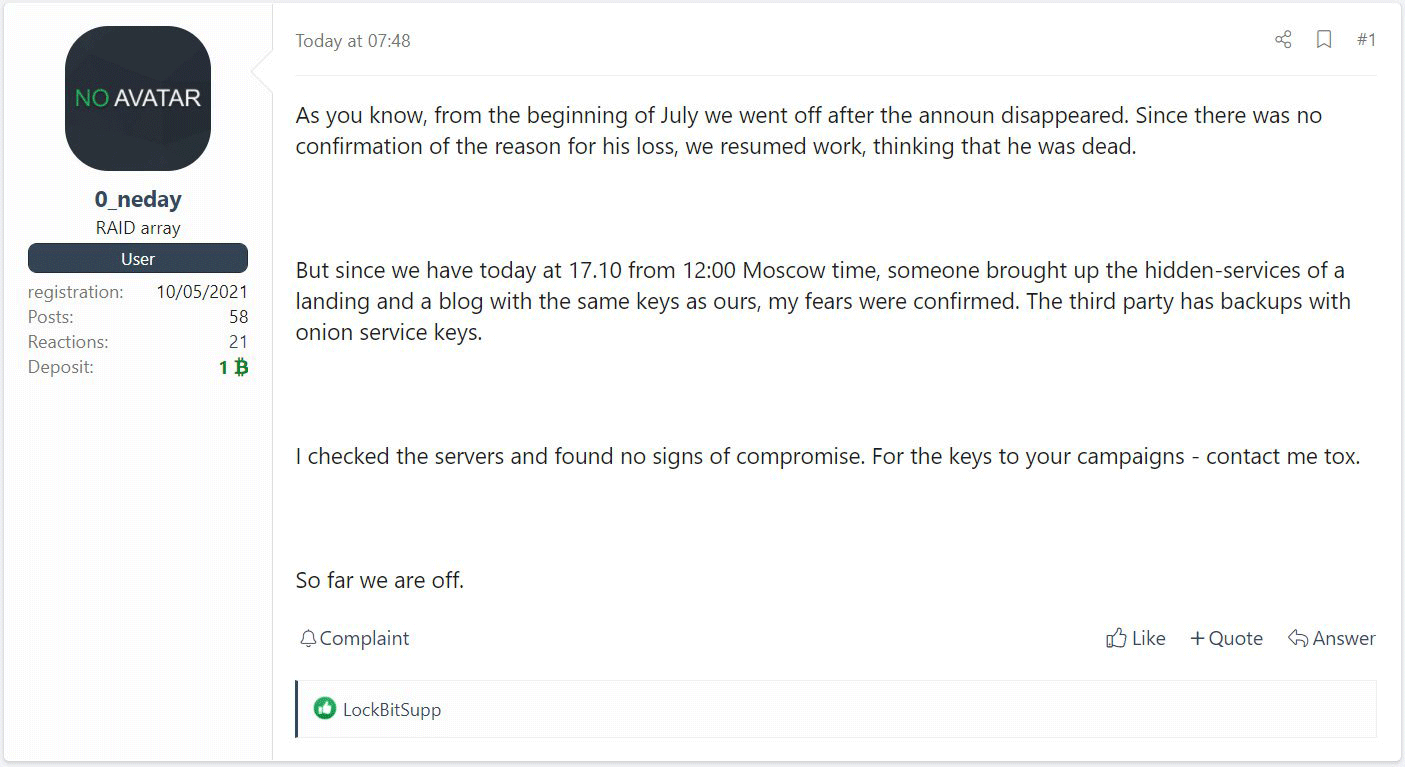
A representative for the gang posted an update to an XSS hacking forum, saying that someone hacked the gang's domains.
It seemed that the unknown person managed to hijack REvil's Tor hidden service that include its .onion domains, as well as the private keys for the Tor sites.
It's also suggested that the unknown hacker may likely has obtained backup of the sites.
"But since we have today at 17.10 from 12:00 Moscow time, someone brought up the hidden-services of a landing and a blog with the same keys as ours, my fears were confirmed. The third party has backups with onion service keys," a threat actor known as '0_neday' posted to the hacking forum.
Despite saying that the unknown hacker had only hacked the domains but didn't compromise the servers, the REvil representative said that the gang is shutting down its operation, likely for real this time.
The threat actor then told the gang's affiliates to contact him for campaign decryption keys via Tox, so affiliates could continue extorting their victims and provide a decryptor if a ransom is paid.
Connections via Tor is different from the ordinary web.
The differences are also seen on the way things work when registering a domain on the Tor hidden service, in which a person needs to generate a private and public key pair to launch a website using an onion domain name.
Owner of an onion domain needs to use the keys to initialize the service.
Here, the owner needs to secure the private key, and ensure that it is only accessible to trusted people. This is because anyone with the private key could simply use the key to launch the same onion service on their own server.
In this case, the unknown individual who managed to hijack REvil's domains, means that the person also has access to REvil's hidden service's private keys.
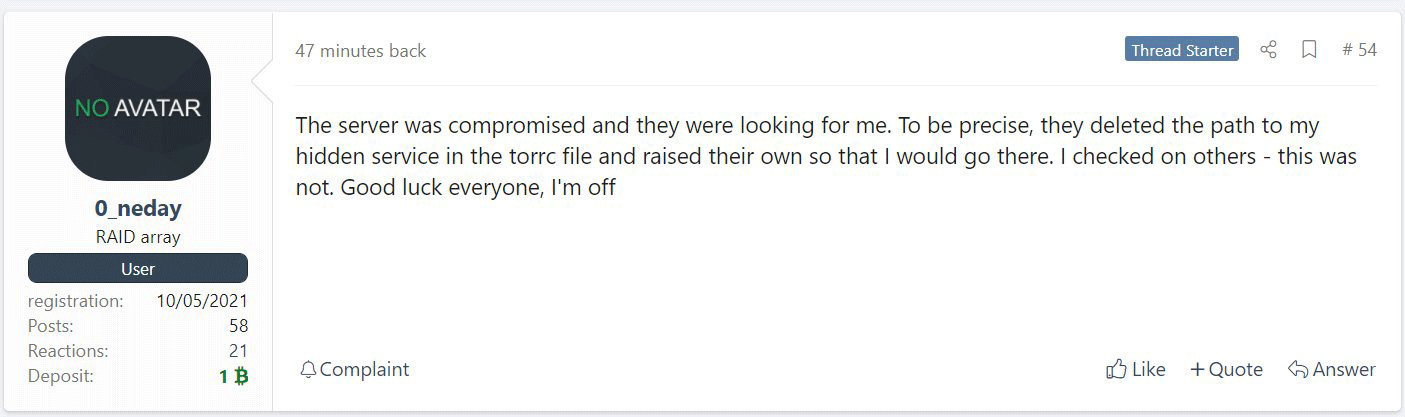
Later, 0_neday posted an update to the same hacking form, saying that the gang's servers were compromised and that whoever did this was targeting the threat actor.
It's suggested that the person behind the hack might be the law enforcements, as the FBI and the authorities have had access to the servers since REvil relaunched them.