With information digitized, not anymore that bad actors are required to present in person to steal, as they can be half way across the globe to launch their malicious attempts.
An emerging group of scammers masquerading as legitimate business executives was found to be the malicious actors behind the more than 200 email-based attacks against Fortune 500 and Global 2000 companies.
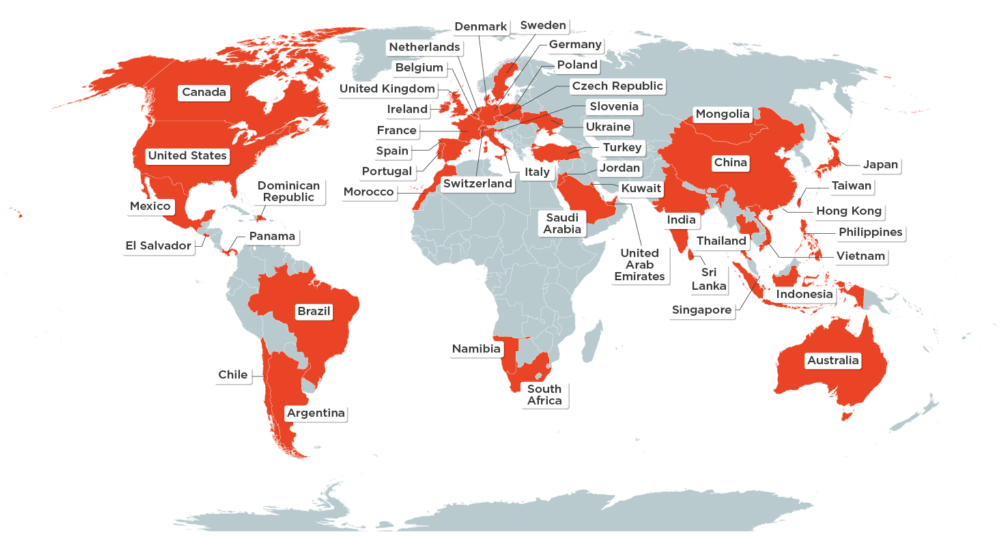
According to a report from security firm Agari, the hacker group that goes with the name 'Cosmic Lynx' has targeted individuals in 46 countries since July 2019.
With the mail-based attacks, the hackers are targeting senior leaders in top companies around the world, by impersonating trusted associates.
Through the emails, the scammers request wire transfers or other form of payments.
It was reported that the Cosmic Lynx group is likely made up of scammers and hackers from Russia.
This is because the group was seen launching many of its attacks during peak hours in Russian time zones.
A document containing wire transfer instructions for payment and a fake non-disclosure agreement, have metadata that showed that they had been saved by a user called 'Serge Devant', the same name as the progressive DJ and producer from St. Petersburg, Russia.
The researchers also tied the group to Russian scammers in part based on the group’s use of TrickBot and Emotet, two widely-used hacking tools designed to steal from banks.
What's more, traced computer IP addresses used in this scheme to other websites that hosted fake documents, also point to Russia.
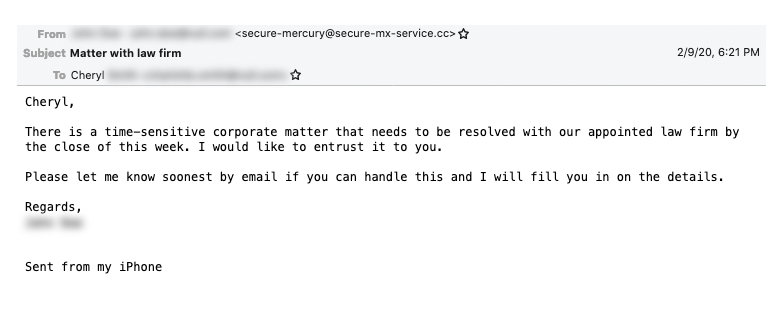
Typically, campaigns launched by the Cosmic Lynx group involve the attackers impersonating the CEO of a fictitious Asian company that the target firm supposedly intends to acquire.
While disguising as a CEO, hackers contact someone in authority from the victim company (usually a vice president, general manager or managing director) and introduce the victim to the would-be legal counsel of the Asian-based firm. Impersonating a 'legal counsel', the scammer then introduces the victim to another scammer that poses as a legitimate lawyer at a British law firm that specializes in mergers and acquisitions.
This 'lawyer' then emails the victim company, usually in a separate thread, with details on how to finalize the transaction.
In one acquired message, the group instructed one victim to send more than $1.5 million as part of a transaction.
And during this 'COVID-19' coronavirus pandemic, the messages can often include salutations, in order to encourage victims to "look beyond the crisis" as businesses prepare for recovery.
“Within every crises, the seeds of opportunity are sowed,” one message reads. “I am please to share that we are seizing the moment and are pressing ahead to acquire the assets of a distressed company. Our legal team is currently working on closing the transaction and I need you to work closely with them on certain time-sensitive issues.”
After receiving the money, the group usually directs it into multiple and separate bank accounts in Hong Kong, Hungary, Portugal and Romania. The money can be then be withdrawn by money mules, or humans to physically take out the cash from the bank before the victim realizes the fraud and cancels the transaction.
Agari that described the group as the first-ever Russian crime ring of this kind, did not disclose how much money the Cosmic Lynx group had fraudulently acquired.
“These sites, which seem to be catering to individuals in Russia and Ukraine, sell a variety of fake Russian-language documents, such as diplomas, birth certificates and death certificates,” the Agari reported.
“While the name of this user can be easily changed to reflect any name, using the name of a Russian DJ, regardless of whether it is legitimate or not, is notable,” the researchers said. “It should be noted that we have no evidence that the real Sarge Devant is associated with Cosmic Lynx activity.”
Cosmic Lynx group is just one of the many hackers that are using the coronavirus pandemic to scam their targets.
The group's malicious tactic is commonly known as a business email compromise (BEC) scam. More often, the tactic is commonly used by suspects with roots from Nigeria.
But unlike most BEC campaigns which tend to be riddled with typos and grammar errors, Cosmic Lynx uses a much better English, with knowledge of some business jargon.
This scam technique has generated profits for the scammers that even the U.S. Department of Justice and other law enforcement agencies have sought to curb the abuse.
In 2019 alone, victims lost $1.7 billion to BEC scams, according to the FBI.