The internet is a growing space, and it will grow larger thanks to the increasing amount of users and nodes.
And here, the VPN industry is growing large alongside it. With faster internet connection and wider coverage, almost any data no matter how large it is, can be sent from one place to another half way across the globe. This evolves communication and transaction to the next level.
But let's not forget the underlying telecommunications networks that connect the links together so data can be exchanged between the nodes.
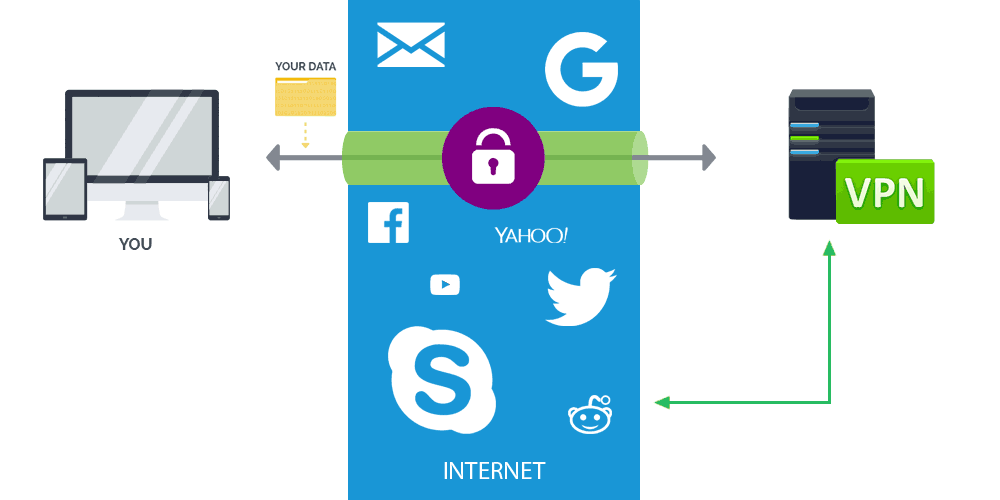
Among the many different network structures that IP addresses can be used to efficiently route messages, is Virtual Private Network.
Also called VPN, it essentially extends a private network across a public network to enable users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. This way, VPN improves privacy and security.
Among the players, is OpenVPN.

Written by James Yonan, OpenVPN was first launched in 2001, as a technique to secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities
OpenVPN allows peers to authenticate each other using pre-shared secret keys, certificates or username/password. When used in a multiclient-server configuration, it allows the server to release an authentication certificate for every client, using signatures and certificate authority.
Using the OpenSSL encryption library extensively, as well as the TLS protocol, OpenVPN has lots of security and control features.
Because it can be implemented on both the client and on the server side, OpenVPN has been ported and embedded to several systems.
But OpenVPN isn't the only one in the business.
WireGuard for example, can be the alternative.
WireGuard has an ambitious goal. In its whitepaper, it's written that:
But can it really compare to the more mature OpenVPN?
The demand of VPN increases as people expect them to be fast and secure. OpenVPN as the older of the two, goes beyond the last-mile or site-to-site protocol. It wants to provide that private, secure and virtualized global internet across many regions, and is also inexpensive.
This is why OpenVPN is considered a more "full suite" solution, by having more things under the hood.
For example, OpenVPN provides high performance VPN protocol offloading to kernel space or dedicated hardware, lightweight network virtualization, fully-meshed VPN sessions, SAML authentication, network threat detection via IDS/IPS/NSM, DDoS protection, multi-region distributed load balancing and failover, MPLS routing, network namespaces, distributed global routing management, virtualized BGP, geolocation-aware routing, and DNS integration.
It markets itself as a secure, virtualized internet in the cloud, and a full suite of enterprise-class tools to manage devices, authentication, routing, network threat detection, load balancing, failover, etc..
In comparison, WireGuard allows providers to optimize their operations, within the scope of the first-generation business model.
WireGuard is capable of handling more concurrent connections and bandwidth per server and lower their overall cost.
But that, without the vast suite of capabilities OpenVPN has to offer.
In terms of speed, WireGuard's approach is based on its simplicity.
It excels in speed also because it is building its VPN system directly inside the Linux kernel, the core part of the Linux operating system.
Since essentially all VPNs run off Linux servers, WireGuard has the potential to change the entire VPN world.
WireGuard also uses an approach called "offloading", or where it can take "heavy lifting" work, such as encryption and forwarding of network packets, and move them to kernel space or specialized hardware that can perform operations at full wire speed.
OpenVPN that according to its whitepaper, is "heavy on functionality," can offload too.
"If you have a modern CPU that supports AES-NI, then the system may be able to offload some of the load," said OpenVPN.
But by having more to offer, OpenVPN's protocol is seen as the slower one between the two.
What's more, OpenVPN uses SSL/TLS, which has conventionally been seen as a user space protocol without a straightforward development path to a high-performance kernel implementation.
So how does OpenVPN compares to WireGuard?
Both have their own protocols that approach problems with different solutions.
WireGuard offers a simple and fast VPN, with lightweight and speedy solution to solve some problems that exist in existing solutions. Unfortunately, its approach in simplicity and speed forced it to sacrifice many features that will be relevant for many users for the foreseeable future.
So can WireGuard be the alternative for OpenVPN? The answer is yes. But can WireGuard replace OpenVPN? the answer is no. Or at least not yet, especially in the corporate world that has more specific demands and requirements.
