With the novel 'COVID-19' coronavirus declared a pandemic, people are urged to stay indoor and keep their distances to help stop the virus' spread.
But since the economy must go on, many companies that have their employees work from home need to have solutions to keep their businesses running. One of which, is by using Zoom.
The cloud-based collaboration tool for enterprise provides a remote conferencing service that combines video conferencing, online meetings, chat, and mobile collaboration.
Since the pandemic, Zoom Video Communications has seen a drastic increase of new monthly active users as millions of employees around the world are working from home.
Its download page experienced a staggering 535% rise in daily traffic, and the service has added roughly 2.22 million new users in just three months alone. This is a massive increase, considering that in the whole 2019, it only added 1.99 million new users.
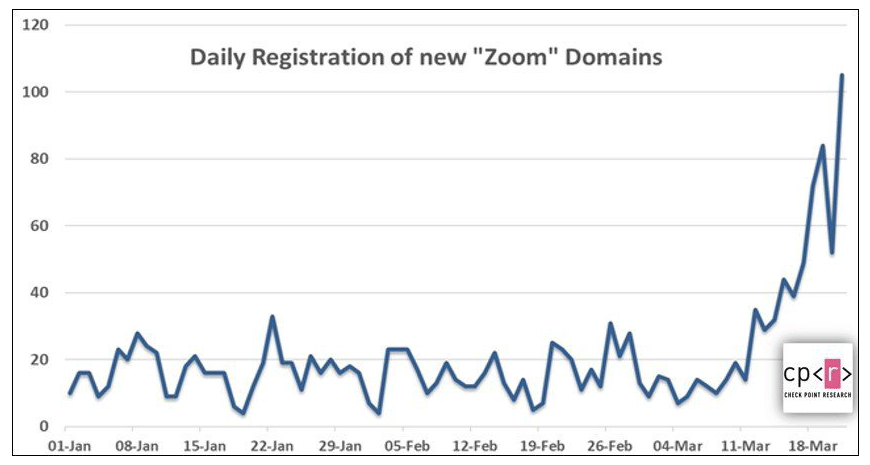
With Zoom's rising popularity among housebound workers and students, hackers are trying to take advantage of its trend.
They started registering hundreds of new Zoom-themed domains for malicious purposes. They too started seeking zero-days-vulnerabilities and bugs to exploit.
They even started creating dedicated channels on Reddit, Discord, and various hacking forums to form raiding parties with other hackers.
Since Facebook's Cambridge Analytica scandal, news and stories about how social media networks lack the privacy and security needed to protect their users were published just about every day.
And Zoom here is seen as one of the less fortunate social apps.
Security researchers and experts have found multiple vulnerabilities in the app in terms of data privacy and security. Some of the bugs are so severe that many researchers have asked users to stay away from the service and find alternatives.
Even the FBI had some words to say about Zoom's mess.
For example, threat actor was able to join active and unprotected Zoom meetings.
Then there was the chance that the meeting’s host had the ability to track participants’ attentiveness through a special feature. And if user record any calls, the administrators of the call, or the company the users are working for, can simply capture all the data, including their operating system, IP address, location data, and device information of each participant.
Zoom said that the tracking feature is off by default, but that apparently was not a satisfying answer, because there are many more issues to come.
Read: How Hackers Piggyback Coronavirus Fears For Their Malicious Campaigns
Later, it was revealed that hackers have been able to hijack video conferences to show porn. To mitigate this 'Zoombombing' issue, users must first disable anyone taking control of the screen, disable file sharing without moderators' permission, and tweak a bunch of other settings, before initiating a call.
Then again, it was discovered that Zoom’s iOS app was found secretly sending user data to Facebook. Zoom removed the Facebook SDK (Software Development Kit) from the Zoom iOS, but to then reveal another issue, in which users' email address and photos were leaked to strangers, if they work under the same company.
Days later, it was reported that Zoom's Windows client could be hacked, where hackers can steal passwords. And there was an issue where Zoom's client for macOS can work stealthily similar to a malware.
Then it was also found that despite the company's claims, communications were not using end-to-end encryption.
After that, again more issues were discovered.
Zero-day bugs allowed a local attacker - someone who already has control of the system - to install malware and gain control of users' microphone and webcam to arbitrarily record footage.
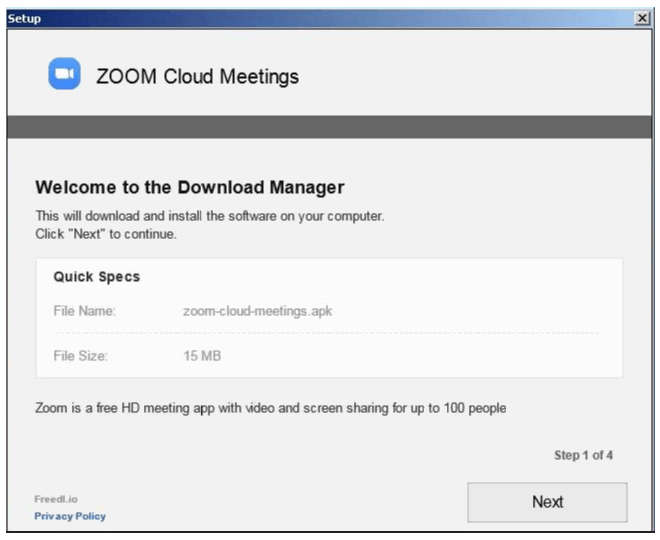
Hackers were also said to have used malicious files using the zoom-us-zoom_##########.exe (# representing various digits) naming scheme which, when executed, will launch InstallCore that will try to download potentially unwanted third-party applications or malicious payloads depending on the attackers' goals.
InstallCore is marked as a potentially unwanted application (PUA) or potentially unwanted program (PUP) by various security solutions and it can, on occasion, disable User Access Control (UAC), add files to be launched on startup, install various browser extensions, and change browsers' configuration and settings.
The InstallCore PUA was also being camouflaged as a Microsoft Teams installer.
All of the above are expected as the outcome of an increasingly popular app.
The bugs may be present before Zoom became a magnet. But all the sudden discoveries were made because the app became popular, as hackers of all kinds are trying to find any security flaws they can exploit. Hackers and threat actors are always on the move, and given by Zoom's sudden surge of users, it's obvious that they too want to benefit from the coronavirus-made trend.
This sudden influx of privacy and security faults can also be the result of a large number of people using the app, and more cybersecurity experts are looking at the app closely.
For its part, Zoom the company is trying to patch and fix the bugs as soon as they're found/reported. The company also paused all the features for 90 days, and committed to enhance the security of the platform, by also enhancing its bug bounty program and conducting a thorough security review via third-party experts.
Founded in 2011 by Eric Yuan, Zoom is a relatively young and small company. And like a lot of other companies trying to build a strong user base, the company was more focused on building features and functionalities instead of looking at its privacy and security.
While Zoom in taking steps to mitigate issues is a welcome move, flaws will keep on being discovered because after all, not product is perfect.
To prevent falling as victims, people should download the app directly from its official Zoom.us website, its page on dedicated mobile app store, and nowhere else.
Users should also rely on their security software to mitigate potential hacks, and update their virus definition regularly for added protection. Users should also be skeptical of emails and files they receive from unknown senders. Common flags to look out for are misspelled words, poor grammar, the addition of random numbers and anything offer a sale or discount.
Users should also try to never click on attachments or links inside suspicious emails.
For users who work from home due to the coronavirus outbreack, they may need to contact their organizations in a separate communication platform, or ask the company's IT team for direction, if they encounter issues or questions.
Or, users can simply ditch Zoom for some other alternatives the market is offering.
Read: Tech Companies Focus On Anything That Is Coronavirus-Related To Stop Misinformation
