The most popular way to hack a device, is to first install a malware into it. After that, as long as the malware remains undetected, things should be easy for hackers.
The hardest part, is to make potential victims to install the malware in the first place. For a long time, hackers use sneaky ways to install malware without victims' knowledge, like for example, through pirated software, or through apps that look legitimate.
And among the many ways hackers can lure victims into their traps, is by showing people a warning that they are infected with a malware. The trick is to make potential victims to download something that supposed to stop the infection.
This has been among the oldest tricks in the book.
But the FluBot, is much more than just that.
This malware spreads like a disease. After it infects devices, it can steal sensitive information, that also include victims' passwords.
First, the FluBot malware send its potential victims text messages to scam them.
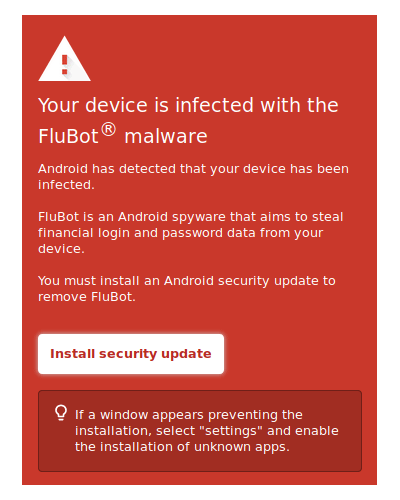
The message said that the recipient's device is infected with FluBot, and that the recipient should download a security update to fix the problem. If the recipient of the SMS proceeds by following the link, they will see a red warning screen claiming that "your device is infected with FluBot® malware" and explicitly states that FluBot is Android spyware that aims to steal financial login and password data.
Other strategies used, include telling potential victims that they have parcels, or claiming that one of the recipient's photos has been uploaded to an online album. The message then provides a link.
These messages are of course a fake.
At this point, the recipient's device is not actually infected with anything at all. No photos of them have been leaked, and no parcel has been sent or waiting. The only reason the malware authors are telling these is because they want the victim to continue with the link that follows.
And by downloading the "security update," the FluBot will then infect the device.
But before it can do anything, FluBot will ask permission in order to spread itself to other victims, to allow the infection chain to continue.
FluBot is an Android malware.
While the SMS and the links to the "security update" can be delivered to iOS-powered devices, FluBot cannot infect Apple devices.
After gaining all the necessary permission, the malware can then have access to all the the financial information it wants to steal.
FluBot has been a persistent malware problem around the world. It acts like a worm, and can easily spread by itself.
However, the only way it can infect, is when the recipient of the message clicks on the link and does what the hackers want.
As long as people don't follow the links, FluBot should not be able to infect their devices.
If a device is infected by FluBot, victims need to perform a factory reset on their phones in order to remove the malware.
