
Malware can come in many forms and types, and sometimes, they have tricks under their sleeves that make them more capable than others.
Cybersecurity researchers said that they have discovered a previously undocumented malware strain dubbed the 'MosaicLoader', when they were analyzing for cracked and pirated software.
The malware has been so named because of its sophisticated abilities that make it capable of evading analysis and reverse-engineering.
On their report, the researchers said that MosaicLoader spreads through search engine optimization (SEO) poisoning, where cybercriminals purchase ads in search engine results to boost their malicious links up on search engine results pages for terms related to pirated software.
According to the researchers at Bitdefender:
"The attackers behind MosaicLoader created a piece of malware that can deliver any payload on the system, making it potentially profitable as a delivery service. The malware arrives on target systems by posing as cracked installers. It downloads a malware sprayer that obtains a list of URLs from the C2 server and downloads the payloads from the received links."
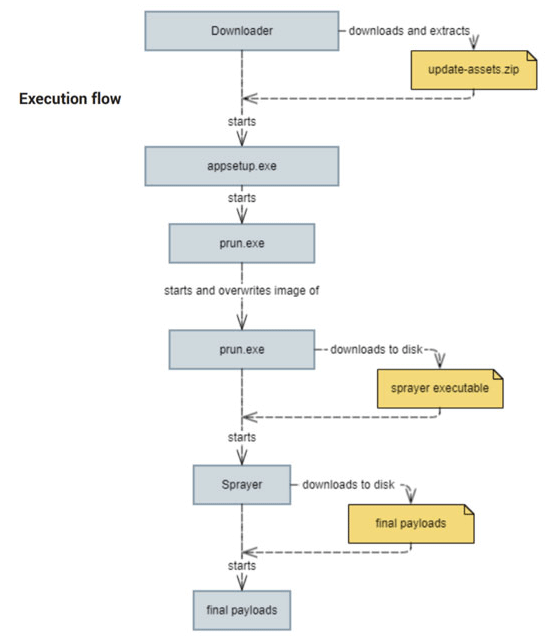
When the malware is successfully downloaded, the malware initially acts as an initial Delphi-based dropper, which masquerades itself as a software installer.
During installation, the malware adds local exclusion to Windows Defender for the two downloaded executables in order to thwart antivirus scanning.
Through the installation of a cracked installer, Windows Defender, the antivirus default on Windows machines, won't detect the malware, fooling users to think that the software they've just downloaded is free from viruses.
The researchers warned that MosaicLoader does not choose a particular region to target. Instead, it only relies on the online ads that generate bogus installers.
“The attackers behind MosaicLoader created a piece of malware that can deliver any payload on the system, making it potentially profitable as a delivery service,” researchers at Bitdefender explained. “It downloads a malware sprayer that obtains a list of URLs from the command-and-control (C2) server and downloads the payloads from the received links.”
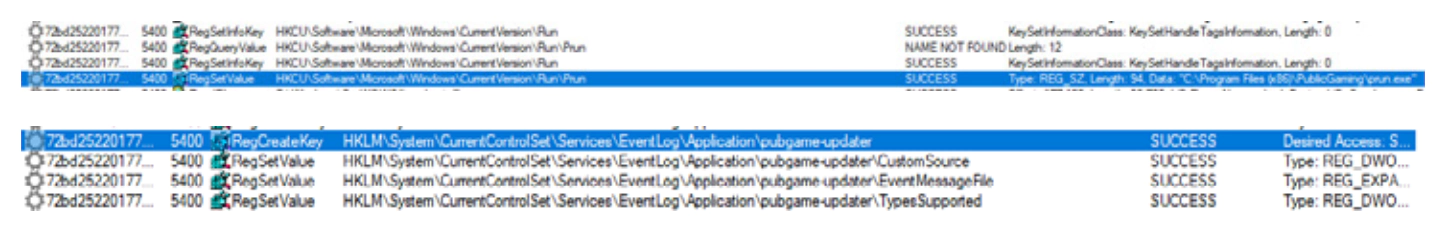
To protect itself, it uses appsetup.exe to achieve persistence on the system, and prun.exe as its method of obfuscation and anti-reverse-engineering techniques.
Lastly, the malware has a sprayer, which downloads a list of malware from a list of URLs controlled by the attackers.
This allows any malware to be installed on the infected system, Bitdefender researchers noted.
This gives MosaicLoader a wide range of capabilities, with compromised systems can be turned into botnets, capable of spreading more sophisticated malware, including both publicly available and customized malware, to obtain, expand, and also maintain unauthorized access to victim computers and networks.
MosaicLoader can also act as a Remote Access Trojan.
In short, MosaicLoader can:
- Mimic file information that is similar to legitimate software.
- Code obfuscation with small chunks and shuffled execution order.
- Payload delivery mechanism infecting the victim with several malware strains.
Since this MosaicLoader malware tricks the users into treating it as a legit installer, people are easily deceived since it shares the same icon with legitimate software.
Furthermore, this malware also passes through the system, and is not detected by Windows Defender antivirus.
Knowing that the malware spreads through cracked and pirated software, the best way to evade this malware is to not install any of those software.
"The best way to defend against MosaicLoader is to avoid downloading cracked software from any source," the researchers said.
"Besides being against the law, cybercriminals look to target and exploit users searching for illegal software," adding that it's essential for people to always "check the source domain of every download to make sure that the files are legitimate."