We store everything on our phones.
From emails, social media accounts, business-related documents, personal photos, to-do lists, and many more. With us becoming even more attached to our devices, the more data we store on our phones, the more vulnerable your privacy becomes.
It's fine if the data stays on your phone. But sadly, smartphones do connect to the internet, and apps may send information about usage and other data to servers elsewhere on the globe.
So no, your data may not be secured as you may have expected.
As technologies change, so does the advice security experts give for how to best stay safe. Here are some of the common ways to secure your digital mobile life so your data stays where you want them to be.

Have Boundaries, And Stick To Them
If you were once a user of a phone that wasn't a smartphone, you must have realized how secured you are with those phones. With no internet connection whatsoever, anything you had on your phone stayed on your phone.
But fast forward to the modern days of the tech where practically everyone with a phone is connected to the vast array of networks we call the internet, data doesn't stay on your phone anymore. You may use cloud storage to keep your photos synced, have allowed certain apps to read your local storage, access the camera and phone contact, and may also have allowed apps to track you wherever you go.
The thing you have to consider, is to stick to the boundaries you set to yourselves.
For example, if you want you contacts to stay on your phone, you have to avoid apps that ask that particular permission. If you want your location to be unknown by giant tech companies, you have to turn off location sharing and GPS. and deny apps that tracks you. if you don't want your private and personal photos to be leaked on the internet, you may want to avoid cloud storage and use local storage instead.
The best way to stay safe on the web, is to set boundaries.
Know in advance what data you’re willing to share with apps and online services, and stick to those limits.
If you follow this rule, the next time you see your favorite app asking your for a permission that changes what you are willing to share, you will be more prepared to answer, and ready to seek for a replacement app.
Manage Passwords
One of the biggest thread to your privacy, is using a weak password.
In the modern days of the web, people use more services than they need. For example, they may have multiple accounts on social media networks, own several email accounts and other accounts for different apps. The worse thing you can do here, is using a weak password.
On top of that, reusing the same password for different services is also one major disadvantage in security stand point.
For your accounts to be protected, and to also minimize the risk of having multiple accounts breached when one has been compromised, the best way is to use a strong password, and never reuse that password again on any other services.
To manage the troubles you may encounter when having many passwords, is to use a password manager software. All you need here, is one very strong password to open your database of passwords.
Or, if you prefer the more traditional method, you can just write down your password on a piece of paper, and keep that paper somewhere safe.
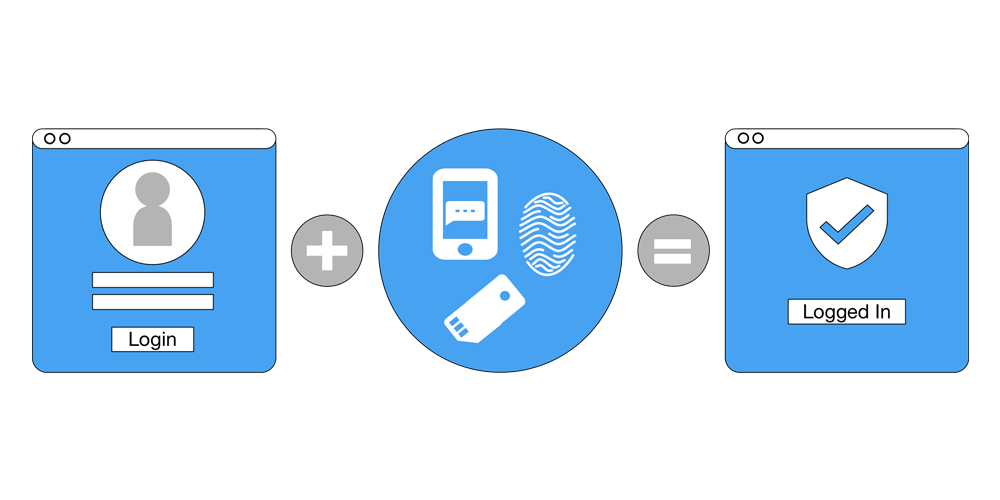
Use Multi-Factor Authentication
Adding an additional step for logging in to your email, social media and financial accounts can add lots of protection.
Multi-factor authentication systems are security measures that needs a second method of authenticating after a successful password authorization. The method can be a text message, a special code from authentication app, or a physical key.
In short, it authenticates you using something you have, something you are, or something you know.
While there can be some weaknesses in using multi-factor authentication, like for example when you lost your phone/key, intercepted SMS or hackers in exploiting voicemail weakness. But still, multi-factor authentication is better than none.
Encrypt Your Data
There was a time when personal and private things can be stored offline on your phone. In the modern days of tech, keeping your data offline seems to be impossible, especially with the increasing amount of them generated, and with the availability of the internet.
Virtually any devices you own or services that you've registered to, can be compromised. Your smartphones can get lost. So how can you secure your data when the potentials of breach is inevitable? The answer is: encryption.
Encrypting your phone's data means that the data cannot be opened, although the phone has been compromised or lost. Without the key to decrypt, the data remains gibberish and unreadable.
Remove Apps You Don't Use
A no brainer. When you have apps you don't use anymore, there is no need to keep them installed on your phone.
First of all, those unused apps will use unnecessary space. If you have limited storage, these unused apps will just eat precious megabytes that otherwise can be used to store something else you really need. Second, those apps may send some technical details about your phone, which in turn can be a privacy issue.
If you don’t use an app anymore, uninstall it from your phone. If you need it again, you can always reinstall it quickly.
But in the meantime, uninstalling unused apps will give some peace of mind as they won't be uselessly tracking you around the world and around the web.
Keep Apps Updated
Just like any products, software can have glitches and vulnerabilities. As a matter of fact, one 'perfect' software on one day may actually be full of security holes the next day after some hackers exploited it.
Software companies don’t always know about all the vulnerabilities in their programs when they uploaded them to app stores. And when they push updates, those companies can never be sure that all users are updating their apps to the newest version.
This is why as users, you need to check whether there are any updates available on your installed apps.
Turn on automatic updates, and make sure that apps you installed can be updated to the newest version as soon as there are updates available.
Further reading: Ways To Protect Your Privacy On The Internet: Your Personal Information Is A Commodity
