Hackers are always on the move to seek potential victims. And in this coronavirus-infected world, cybercriminals are more than happy to leverage the trend.
Among the many ways, hackers have piggybacked the big names of health, like the WHO, created a coronavirus dashboard map, and others.
Due to the variety of attacks, which mostly leverage some sorts of malware, businesses and organizations should always be on their toes to anticipate those forms of attacks.
Microsoft is one of the biggest players in the technology sector, and here, the company has decided to open source its COVID-19 threat intelligence.
By sharing what it knows, Microsoft hopes that it can provide the foundation for people to better defense themselves from hackers.
Using its COVID-19 threat intelligence, the entire security intelligence community can be more proactive in protecting, detecting and defending against coronavirus-related attacks.
In a blog post, Microsoft said that:
Microsoft said that its own security products, such as its Microsoft Defender Advanced Threat Protection (ATP), are already equipped with built-in protections against coronavirus-related attacks and other threats.
The company has also published a detailed guidance titled “Responding to COVID-19 together” to help businesses and organizations combat them as well.
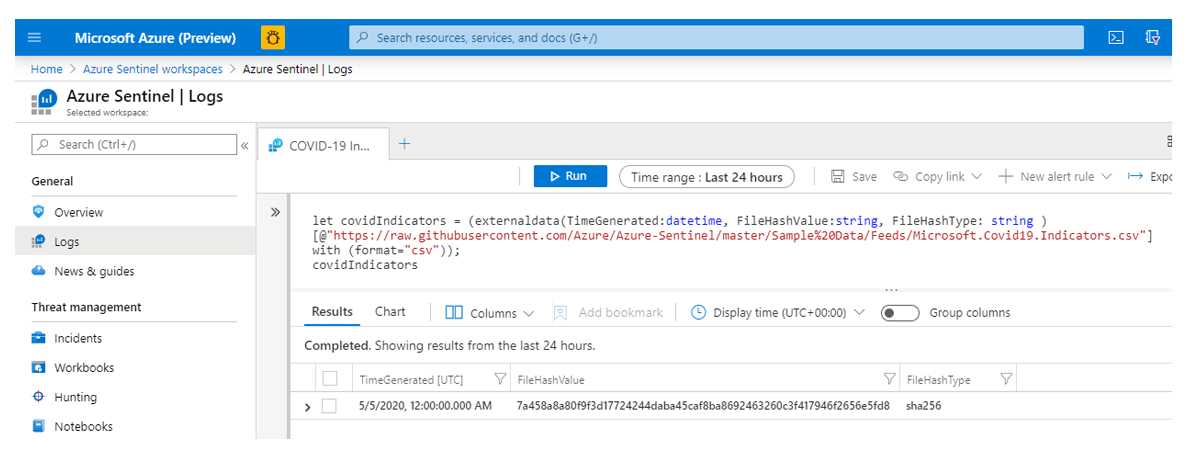
"Our threat experts are sharing examples of malicious lures and we have enabled guided hunting of COVID-themed threats using Azure Sentinel Notebooks," said Microsoft.
In the blog post, Microsoft explained that it will continue to maintain its threat intelligence feed during the peak of the coronavirus outbreak, saying that:
Microsoft in open-sourcing its COVID-19 threat intelligence is to make sure that others that don't benefit from its products, can still be protected against coronavirus-related threats.
"Today, we take our COVID-19 threat intelligence sharing a step further by making some of our own indicators available publicly for those that are not already protected by our solutions," said Microsoft.
By putting the project open-source, Microsoft is taking a step forward in making sure that it can raise awareness about how hackers are shifting their methods of attacks and techniques, how to spot them, and how others can hunt for threats on their own.
The company's indicators have been available in the Azure Sentinel GitHub, as well as through the Microsoft Graph Security API.
As for Microsoft Enterprise customers that use MISP for storing and sharing threat intelligence, they can access these indicators via a MISP feed.