A person that goes with the name gnosticplayers got hold of more than 700 million accounts from 24 hacked websites. And here, the seller was selling the information on the dark web.
The information which included the accounts' holder names, email addresses and hashed passwords, can be purchased from the Dream Market cyber-souk, located in the Tor network.
Initially, information taken from 16 websites were up for sale. They were:
- Dubsmash: 161,549,210 accounts for 0.549 BTC ($1,976). 11GB stolen in December 2018.
- MyFitnessPal: 150,633,038 accounts for 0.289 BTC ($1,040). 3.5GB stolen in February 2018.
- MyHeritage: 92,284,478 accounts for 0.549 BTC ($1,976). 3.6GB stolen in October 2017.
- ShareThis: 41,028,098 accounts for 0.217 BTC ($780). 2.7GB stolen in early July 2018.
- HauteLook: 28 million accounts for 0.217 BTC ($780). 1.5GB stolen in 2018.
- Animoto: 25,402,283 accounts for 0.318 BTC ($1,144). 2.1GB stolen in 2018.
- EyeEm: 22,360,765 accounts for 0.289 BTC ($1,040). 1.7GB stolen in February 2018.
- 8fit: 20,180,667 accounts for 0.2025 BTC ($728). 1.9GB stolen in 2018.
- Whitepages: 17,775,679 accounts for 0.434 BTC ($1560). 2.9GB stolen in 2016.
- Fotolog: 16 million accounts for 0.52 BTC ($1,872). 5.9GB stolen in December 2018.
- 500px: 14,870,304 accounts for 0.217 BTC ($780). 1.5GB stolen in July 2018.
- Armor Games: 11,013,617 accounts for 0.2749 BTC ($988). 1.8GB stolen in late December 2018.
- BookMate: 8,026,992 accounts for 0.159 BTC ($572). 1.7GB stolen in July 2018.
- CoffeeMeetsBagel: 6,174,513 accounts for 0.13 BTC ($468). 673MB stolen in mid-2018.
- Artsy: 1,070,000 accounts for 0.0289 BTC ($104). 184MB stolen in April 2018
- DataCamp: 700,000 accounts for 0.013 BTC ($46.8). 82MB stolen in December 2018.
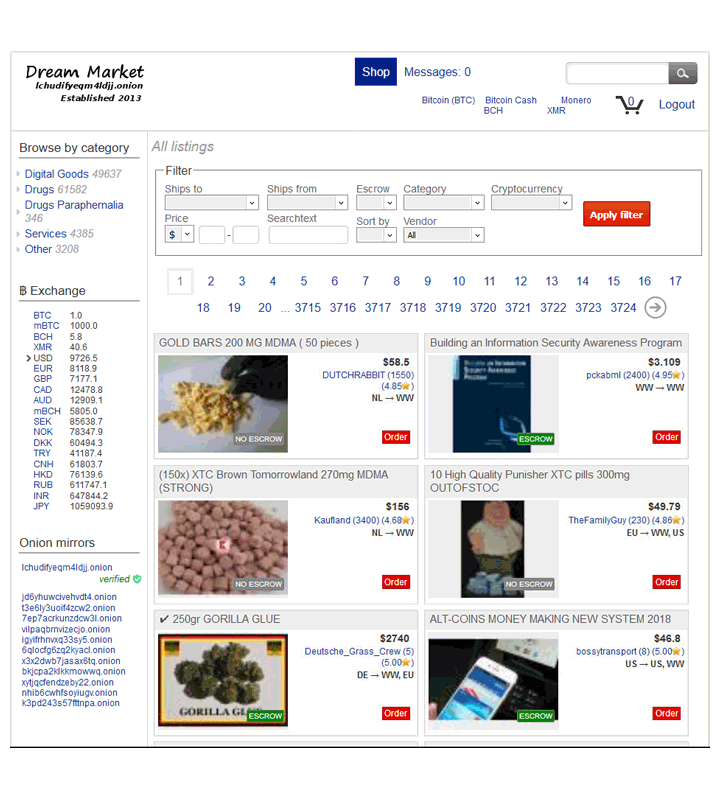
These were up for sale for less than $20,000 in Bitcoin. But later the entries were removed from the market to avoid too many customers buying them and losing control of the "merchandise".
Over the weekend, the underground market experienced a distributed denial-of-service attack that happened in briefly, putting the market rather quiet. But when it returned to normal, the seller added 8 more websites containing 127 million records.
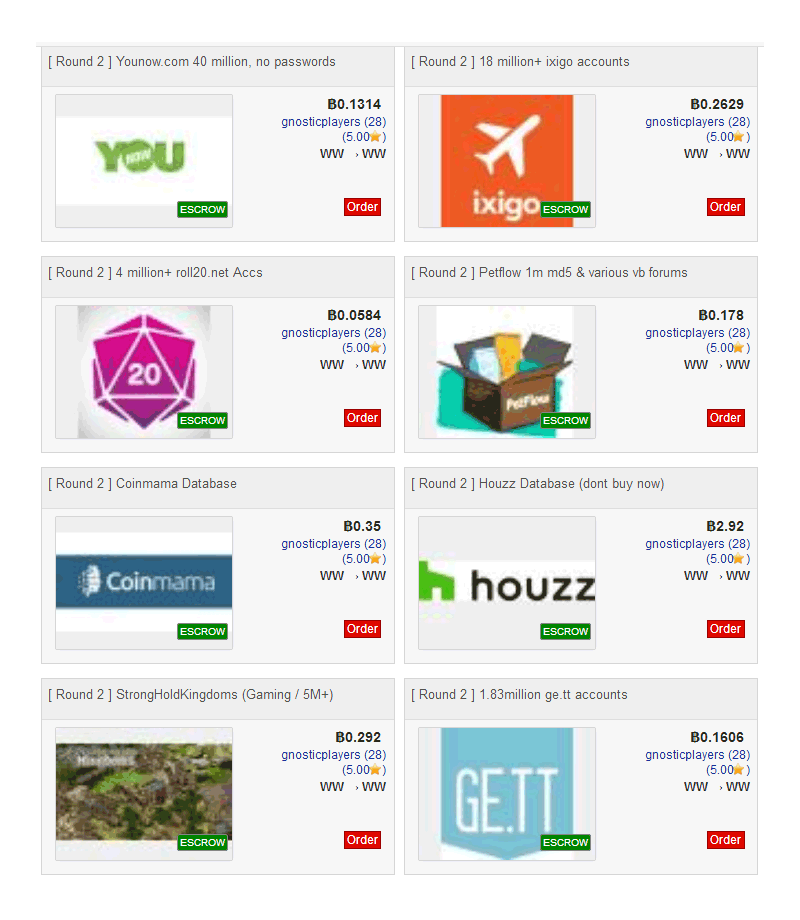
They included: YouNow, StrongHoldKingdoms, Roll20, Petflow, Ixigo, Houzz, Ge.tt and CoinMama.
The seller asked the equivalent of $14,500 in Bitcoin.
But again, just like the first round, this second round was later removed. The seller said that "All my listings have been removed, to avoid them being bought so many times and being leaked, as a respect for my buyers. But don't worry, next round of breaches coming soon."
While some of the websites affected have already disclosed their data breach, some like 500px, only became aware of the incident just before this massive leak was discovered.
According to 500px:
"Our engineers immediately launched a comprehensive review of our systems and have since taken every precaution to secure them. All areas of vulnerability have been identified and fixed during our internal investigation, and we’ve found no evidence to date of any recurrence of the issue."
All of the databases were touted separately by the hacker, who said that he/she exploited security vulnerabilities within web apps to gain remote-code execution and then extract user account data.
Buyers are more likely to be spammers and credential stuffers, which is why the copies were relatively cheap to buy.
The stuffers can take usernames and passwords from one site to log into accounts on other websites where the users have used the same credentials.
According to The Register that received a sample of the multi-gigabyte databases, said that they appear to be legit
"There are a few other bits of information, depending on the site, such as location, personal details, and social media authentication tokens. There appears to be no payment or bank card details in the sales listings," said The Register.
As for passwords, they were hashed only using the ]MD5 algorithm, which is not that difficult to crack.
A spokesperson at MyHeritage confirmed the samples are real. CoffeeMeetsBagel, 8fit, 500px, DataCamp, and EyeEm have also confirmed their account data was stolen from their servers and put up for sale in the seller's collection on the dark web's Dream Market.