Keeping up with the "smart" devices trend, home appliance manufacturers have made their devices smarter by making them capable of receiving commands from voice or smartphones.
For improved experience, these devices can connect to the internet, opening the new possibilities that are otherwise impossible.
When the first smart-home device hit the market, some people started wondering whether IoT devices can be trusted. After all, they work similarly to smartphones, and smartphones collect bunch of information. However, there weren't that many studies and researches that go deep into the details to this smart-home ecosystem.
That until a team of researchers from Northeastern University and the Imperial College of London, wanted to know more about how these devices work behind-the-scene.
David Choffnes, a professor of computer science at Northeastern, was one of the researchers. He said that his previous work looking at the data collection and dissemination habits of mobile apps led him to expect that similar data gathering and data sending practices also happen on smart-home devices.
At the highlight of their research, the team found that smart-home devices are indeed collecting sensitive user data, and sending them to third-parties.

The team found that a variety of internet-connected devices collected and distributed data to companies other than the manufacturers themselves - even if the consumers of the devices didn't interact with those third-party companies.
"Nearly all TV devices in our testbeds contacts Netflix even though we never configured any TV with a Netflix account," the researchers wrote.
As the findings show, the researchers said that user data are sent to companies, including Google, Facebook and Amazon, as well as others, like Mixpanel, a company that provides product and behavioral analytics.
One good thing is that, those smart-home devices use encryption for protection. While this is a good thing on the consumers' side, but it also makes it harder for anyone to see and know what information the devices are sending to third-parties.
The takeaway is that, everything from smart TVs to internet-connected refrigerators, tend to collect and share more data than other devices.
"You can usually install apps and as a result you're going to see somewhat similar behavior as you do on a mobile device," Choffnes said.
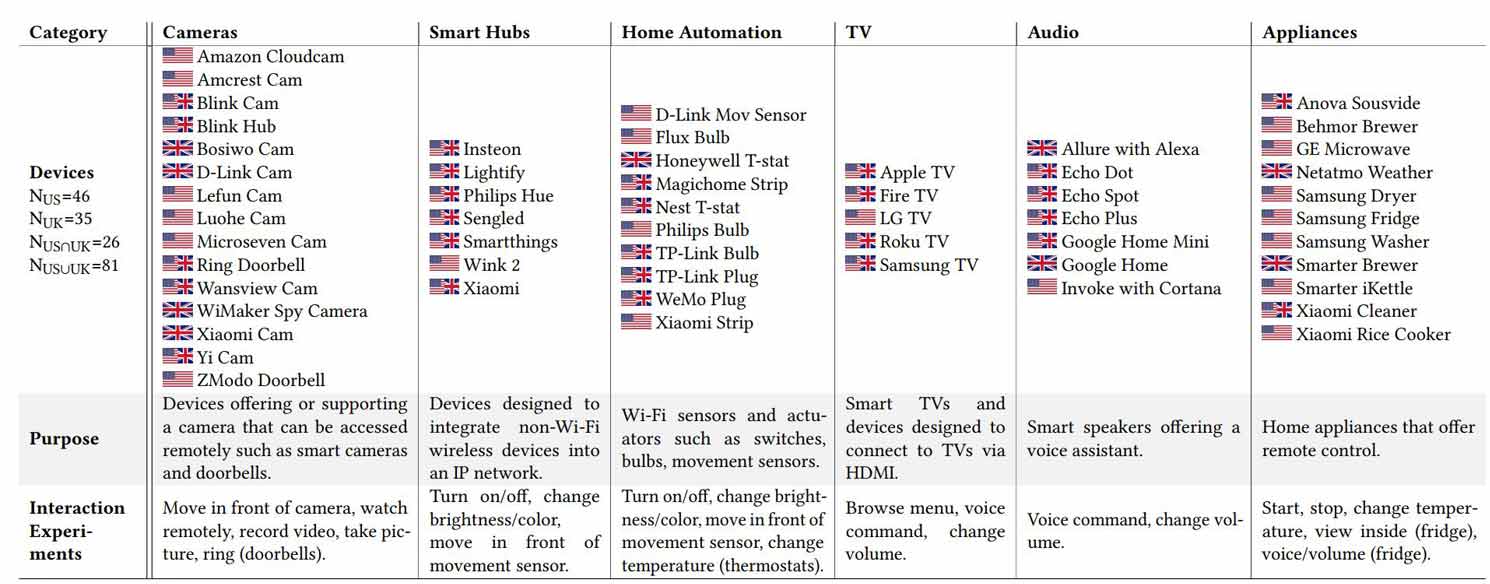
Here, Choffnes and his team concluded their findings after analyzing 81 different IoT products (46 devices from the U.S., and 35 devices from the UK, ranging from cameras, smart hubs, home automation, smart TVs, smart audio speakers, and smart home appliances), to characterize what services they attempt to connect with, what communications can be inferred from these connections, and the degree of encryption used to protect customers.
As for what was being leaked to third-parties:
"In both our labs we found that Magichome Strip is sending its MAC address in plaintext to a domain hosted on Alibaba. Interestingly, the Insteon hub was sending its MAC address in plaintext to an EC2 domain, but only from the UK lab. We did not find similar behavior in the US lab. Interestingly, each time the Xiaomi camera detected a motion, its MAC address, the hour and the date of the motion (in plaintext) was sent to an EC2 domain. We also noted that a video was included on the payload."
Choffnes said that consumers really don't have that many options to prevent these practices from happening, aside from disconnecting them from the internet, or not using those devices entirely. This is because at the moment of his finding, there isn't any tools, like tracker blockers for smart appliances, for example.